Keywords
Computer Science and Digital Science
- A1.2. Networks
- A1.2.5. Internet of things
- A1.2.6. Sensor networks
- A1.2.7. Cyber-physical systems
- A1.3. Distributed Systems
- A1.4. Ubiquitous Systems
- A2.3. Embedded and cyber-physical systems
- A2.3.2. Cyber-physical systems
- A2.5.1. Software Architecture & Design
- A2.5.3. Empirical Software Engineering
- A2.5.4. Software Maintenance & Evolution
- A2.6. Infrastructure software
- A2.6.1. Operating systems
- A2.6.2. Middleware
- A4.8. Privacy-enhancing technologies
- A5.11. Smart spaces
- A5.11.1. Human activity analysis and recognition
- A5.11.2. Home/building control and interaction
Other Research Topics and Application Domains
- B3.1. Sustainable development
- B3.1.1. Resource management
- B4.4. Energy delivery
- B4.4.1. Smart grids
- B4.5.2. Embedded sensors consumption
- B6.1. Software industry
- B6.1.1. Software engineering
- B6.1.2. Software evolution, maintenance
- B6.2.2. Radio technology
- B6.3.3. Network Management
- B6.4. Internet of things
- B7.2. Smart travel
- B7.2.1. Smart vehicles
- B7.2.2. Smart road
- B8.1. Smart building/home
- B8.1.1. Energy for smart buildings
- B8.1.2. Sensor networks for smart buildings
- B8.2. Connected city
- B8.5.2. Crowd sourcing
- B8.5.3. Collaborative economy
- B9.8. Reproducibility
- B9.10. Privacy
1 Team members, visitors, external collaborators
Research Scientists
- Paul Couderc [Inria, Researcher]
- Christophe Couturier [IMT Atlantique, Researcher]
Faculty Members
- Jean-Marie Bonnin [Team leader, IMT Atlantique, Professor, HDR]
- Yoann Maurel [Univ de Rennes I, Associate Professor]
- Frédéric Weis [Univ de Rennes I, Associate Professor, HDR]
Post-Doctoral Fellow
- Laudin Molina [IMT Atlantique]
PhD Students
- Indra Er [Indonesia Endowment Fund for Education - Indonésie, until Apr 2020]
- Alexandre Rio [Okwind, CIFRE, until Feb 2020]
Technical Staff
- Elisa Blanchard [IMT Atlantique, Engineer]
- Alexis Girard [Inria, Engineer, until Oct 2020]
- Nicolas Harel [Inria, Engineer]
Interns and Apprentices
- Ronan Buron [Inria, from Mar 2020 until Aug 2020]
- Brandon Largeau [Inria, from May 2020 until Aug 2020]
Administrative Assistant
- Fabienne Cuyollaa [Inria]
2 Overall objectives
2.1 Presentation
The technologies necessary for the development of pervasive applications are now widely available and accessible for many uses: short/long-range and low energy communications, a broad variety of visible (smart objects) or invisible (sensors and actuators) objects, as well as the democratization of the Internet of Things (IoT). Large areas of our living spaces are now instrumented. The concept of Smart Spaces is about to emerge, based upon both massive and apposite interactions between individuals and their everyday working and living environments: residential housing, public buildings, transportation, etc. The possibilities of new applications are boundless. Many scenarios have been studied in laboratories for many years and, today, a real ability to adapt the environment to the behaviors and needs of users can be demonstrated. However mainstream pervasive applications are barely existent, at the notable exception of the ubiquitous GPS-based navigators. The opportunity of using vast amounts of data collected from the physical environments for several application domains is still largely untapped. The applications that interact with users and act according to their environment with a large autonomy are still very specialized. They can only be used in the environment they had especially been developed for (for example "classical" home automation tasks: comfort, entertainment, surveillance). They are difficult to adapt to increasingly complex situations, even though the environments in which they evolve are more open, or change over time (new sensors added, failures, mobility etc.).
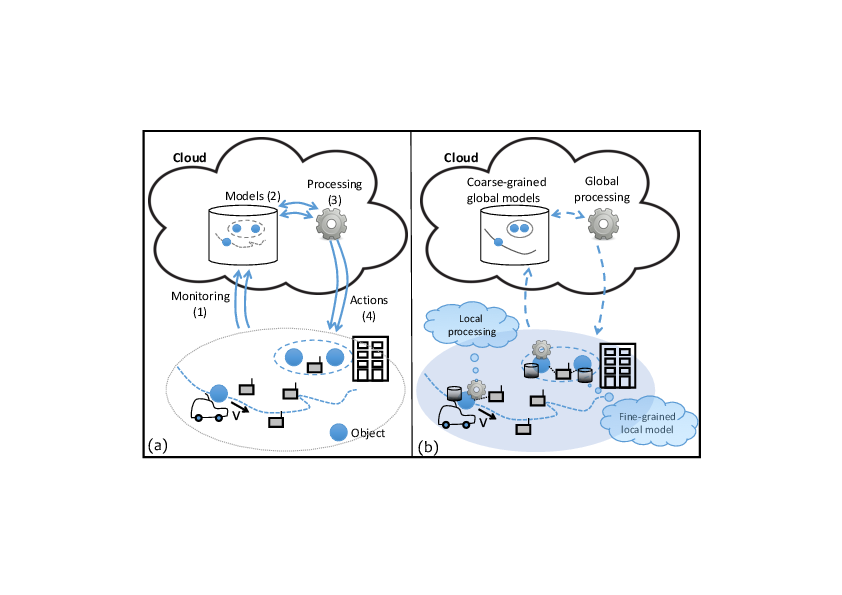
Developing applications and services that are ready to deploy and evolve in different environments should involve a significant cost reduction. Unfortunately, designing, testing and ensuring the maintenance as well as the evolution of a pervasive application remain very complex. In our view, the lack of resources by which properties of the real environment are made available to application developers is a major concern. Building a pervasive application involves implementing one or more logical control loops which include four stages (see figure 1-a): (1) data collection in the real environment, (2) the (re)construction of information that is meaningful for the application and (3) for decision making, and finally, (4) action within the environment. While many decision-algorithms have been proposed, the collection and construction of a reliable and relevant perception of the environment and, in return, action mechanisms within the environment still pose major challenges that the Tacoma/Ease project is prepared to deal with.
Most current solutions are based on a massive collection of raw data from the environment, stored on remote servers. Figure 1-a illustrates this type of approach. Exposure of raw sensor values to the decision-making process does not allow to build relevant contexts that a pervasive application actually needs in order to shrewdly act/react to changes in the environment. So, the following is left up to the developer:
- To characterize more finely raw data beyond its simple value, for example, the acquisition date, the nature of network links crossed to access the sensor, the durability and accuracy of value reading, etc.
- To exploit this raw data to calculate a relevant abstraction for the application, such as, whether the room is occupied, or whether two objects are in the same physical vicinity.
- To modify the environment when possible.
Traditional software architectures isolate the developer from the real environment that he has to depict according to complex, heavy and expensive processes. However, objects and infrastructure integrated into user environments could provide a more suitable support to pervasive applications: description of the actual system's state can be richer, more accurate, and, simultaneously, easier to handle; the applications' structure can be distributed by being built directly into the environment, facilitating scalability and resilience by the processing autonomy; finally, moving processing closer to the edge of the network avoids major problems of data sovereignty and privacy encountered in infrastructures very dependent on the cloud. We strongly believe in the advantages of specific approaches to the fields of edge computing and fog computing, which will reveal themselves with the development of Smart Spaces and an expansive growth of the number of connected objects. Indeed, ensuring the availability and reliability of systems that remain frugal in terms of resources will become in the end a major challenge to be faced in order to allow proximity between processing and end-users. Figure 1-b displays the principle of "using data at the best place for processing". Fine decisions can be made closer to the objects producing and acting on the data, local data characterization and local processing de-emphasize the computing and storage resources of the cloud (which can be used for example to store selected/transformed data for global historical analysis or optimization).
Ease aims at developing a comprehensive set of new interaction models and system architectures to considerably help pervasive application designers in the development phase with the side effect to ease the life cycle management. We follow two main principles:
- Leveraging local properties and direct interactions between objects, we would be able to enrich and to locally manage data produced in the environment. The application would then be able to build their knowledge about their environment (perception) in order to adjust their behavior (e.g. level of automation) to the actual situation.
- Pervasive applications should be able to describe requirements they have on the quality of their environmental perception. We would be able to achieve the minimum quality level adapting the diversity of the sources (data fusion/aggregation), the network mechanisms used to collect the data (network/link level) and the production of the raw data (sensors).
3 Research program
3.1 Collecting pertinent information
In our model, applications adapt their behavior (for instance, the level of automation) to the quality of their perception of the environment. This is important to alleviate the development constraint we usually have on automated systems. We "just" have to be sure a given process will always operate at the right automation level given the precision, the completeness or the confidence it has on its own perception. For instance, a car passing through a crossing would choose its speed depending on the confidence it has gained during perception data gathering. When it has not enough information or when it could not trust it, it should reduce the automation level, therefore the speed, to only rely on its own sensors. Such an adaptation capability shift the requirements from the design and deployment (availability, robustness, accuracy, etc.) to the assessment of the environment perception which we aim to facilitate in this first research axis.
Data characterization. The quality (freshness, accuracy, confidence, reliability, confidentiality, etc.) of the data are of crucial importance to assess the quality of the perception and therefore to ensure proper behavior. The way data is produced, consolidated, and aggregated while flowing to the consumer has an impact on its quality. Moreover, part of these quality attributes requires to gather information at several communication layers from various entities. For this purpose, we want to design lightweight cross-layer interactions to collect relevant data. As a "frugality" principle should guide our approach, it is not appropriate to build all the attributes we can imagine. It is therefore necessary to identify attributes relevant to the application and to have mechanisms to activate/deactivate at run-time the process to collect them.
Data fusion. Raw data should be directly used only to determine low-level abstraction. Further help in abstracting from low-level details can be provided by data fusion mechanisms. A good (re)construction of meaningful information for the application reduces the complexity of the pervasive applications and helps the developers to concentrate on the application logic rather on the management of raw data. Moreover, the reactivity required in pervasive systems and the aggregation of large amounts of data (and its processing) are antagonists. We study software services that can be deployed closer to the edge of the network. The exploration of data fusion techniques will be guided by different criteria: relevance of abstractions produced for pervasive applications, anonymization of exploited raw data, processing time, etc.
Assessing the correctness of the behavior. To ease the design of new applications and to align the development of new products with the ever faster standard developments, continuous integration could be used in parallel with continuous conformance and interoperability testing. We already participate in the design of new shared platforms that aims at facilitating this providing remote testing tools. Unfortunately, it is not possible to be sure that all potential peers in the surrounding have a conforming behavior. Moreover, upon failure or security breach, a piece of equipment could stop operating properly and lead to global mis-behavior. We want to propose conceptual tools for testing at runtime devices in the environment. The result of such conformance or interoperability tests could be stored safely in the environment by an authoritative testing entity. Then the application could interact with the device with higher confidence. The confidence level of a device could be part of the quality attribute of the information it contributed to generate. The same set of tools could be used to identify misbehaving device for maintenance purposes or to trigger further testing.
3.2 Building relevant abstraction for new interactions
The pervasive applications are often designed in an ad hoc manner depending on the targeted application area. Ressources (sensors / actuators, connected objets, etc.) are often used in silos which complexifies the implementation of rich pervasive computing scenarios. In the second research axis, we want to get away from technical aspects to identify common and reusable system mechanisms that could be used in various applications.
Tagging the environment. Information relative to the environment could be stored by the application itself, but it could be complex to manage for mobile applications since it could cross a large number of places with various features. Moreover the developer has to build his own representation of information especially when he wants to share information with other instances of the same application or with other applications. A promising approach is to store and to maintain this information associated to an object or to a place, in the environment itself. The infrastructure should provide services to application developers: add/retrieve information in the environment, share information and control who can access it, add computed properties to object for further usage. We want to study an extensible model to describe and augment the environment. Beyond a simple distributed storage, we have in mind a new kind of interaction between pervasive applications and the changing environment and between applications themselves.
Taking advantages of the spatial relationships. To understand the world they have to interact with, pervasive applications often have to (re)build a model of it from the exchange they have with others or from their own observations. A part of the programmer's task consists in building a model of the spatial layout of the objects in the surrounding. The term layout can be understood in several ways: the co-location of multiple objects in the same vicinity, the physical arrangement of two objects relative to each other, or even the crossing of an object of a physical area to another, etc. Determining remotely these spatial properties (see figure 1-a) is difficult without exchanging a lot of information. Properties related to the spatial layout are far easier to characterize locally. They could be abstracted from the interaction pattern without any complex virtual representation of the environment (see figure 1-b). We want to be able to rely on this type of spatial layout in a pervasive environment. In the prior years, the members of Ease already worked on models for processing object interactions in the physical world to automatically trigger processing. This was the case in particular of the spatial programming principle: physical space is treated as a tuple-space in which objects are automatically synchronized according to their spatial arrangement. We want to follow this approach by considering richer and more expressive programming models.
3.3 Acting on the environment
The conceptual tools we aim to study must be frugal: they use as few as possible resources, while having the possibility to use much more when it is required. Data needed by an application are not made available for "free"; for example, it costs energy to measure a characteristic of the environment, or to transmit it. So this "design frugality" requires a fine-grained control on how data is actually collected from the environment. The third research axis aims at designing solutions that give this control to application developers by acting on the environment.
Acting on the data collection. We want to be able to identify which information are really needed during the perception elaboration process. If a piece of data is missing to build a given information with the appropriate quality level, the data collection mechanism should find relevant information in the environment or modify the way it aggregates it. These could lead to a modification of the behavior of the network layer and the path the piece of data uses in the aggregation process.
Acting on object interactions. Objects in the environment could adapt their behavior in a way that strongly depends on the object itself and that is difficult to generalize. Beyond the specific behaviors of actuators triggered through specialized or standard interfaces, the production of information required by an application could necessitate an adaptation at the object level (eg. calibration, sampling). The environment should then be able to initiate such an adaption transparently to the application, which may not know all objects it passes by.
Adapting object behaviors. The radio communication layers become more flexible and able to adapt the way they use energy to what is really required for a given transmission. We already study how beamforming techniques could be used to adapt the multicast strategy for video services. We want to show how playing with these new parameters of transmissions (e.g. beamforming, power, ...) allows to control spatial relationships objects could have. There is a tradeoff to find between the capacity of the medium, the electromagnetic pollution and the reactivity of the environment. We plan to extend our previous work on interface selection and more generally on what we call opportunistic networking.
4 Application domains
4.1 Pervasive applications in Smart Building
A Smart Building is a living space equipped with information-and-communication-technology (ICT) devices conceived to collaborate in order to anticipate and respond to the needs of the occupants, working to promote their comfort, convenience, security and entertainment while preserving their natural interaction with the environment.
The idea of using the Pervasive Computing paradigm in the Smart Building domain is not new. However, the state-of-the-art solutions only partially adhere to its principles. Often the adopted approach consists in a heavy deployment of sensor nodes, which continuously send a lot of data to a central elaboration unit, in charge of the difficult task of extrapolating meaningful information using complex techniques. This is a logical approach. Ease proposed instead the adoption of a physical approach, in which the information is spread in the environment, carried by the entities themselves, and the elaboration is directly executed by these entities "inside" the physical space. This allows performing meaningful exchanges of data that will thereafter need a less complicated processing compared to the current solutions. The result is a smart environment that can, in an easier and better way, integrate the context in its functioning and thus seamlessly deliver more useful and effective user services. Our contribution aims at implementing the physical approach in a smarter environment, showing a solution for improving both comfort and energy savings.
4.2 Automation in Smart City
The domain of Smart Cities is still young but it is already a huge market which attracts number of companies and researchers. It is also multi-fold as the words "smart city" gather multiple meanings. Among them one of the main responsibilities of a city, is to organize the transportation of goods and people. In intelligent transportation systems (ITS), ICT technologies have been involved to improve planification and more generally efficiency of journeys within the city. We are interested in the next step where efficiency would be improved locally relying on local interactions between vehicles, infrastructure and people (smartphones).
For the future autonomous vehicle are now in the spotlight, since a lot of works has been done in recent years in automotive industry as well as in academic research centers. Such unmanned vehicles could strongly impact the organisation of the transportation in our cities. However, due to the lack of a definition of what is an "autonomous" vehicle, it is still difficult to see how these vehicles will interact with their environment (eg. road, smart city, houses, grid, etc.). From augmented perception to fully cooperative automated vehicle, the autonomy covers various realities in terms of interaction the vehicle relies on. The extended perception relies on communication between the vehicle and surrounding roadside equipments. That helps the driving system to build and maintain an accurate view of the environment. But at this first stage the vehicle only uses its own perception to make its decisions. At a second stage, it will take advantages of local interaction with other vehicles through car-to-car communications to elaborate a better view of its environment. Such "cooperative autonomy" does not try to reproduce the human behavior anymore, it strongly relies on communication between vehicles and/or with the infrastructure to make decision and to acquire information on the environment. Part of the decision could be centralized (almost everything for an automatic metro) or coordinated by a roadside component. The decision making could even be fully distributed but this put high constraints on the communications. Automated vehicles are just an example of smart city automated processes that will have to share information within the surrounding to make their decisions.
4.3 Pervasive applications in uncontrolled environnements
Some limitations of existing RFID technology become challenging: unlike standard RFID application scenarios, pervasive computing often involves uncontrolled environment for RFID, where tags and reader have to operate in much more difficult situations that those usually encountered or expected for classical RFID systems.
RFID technology is to avoid missing tags when reading multiple objects, as reading reliability is affected by various effects such shadowing or wave power absorption by some materials. The usual applications of RFID operate in a controlled environment in order to reduce the risk of missing tags while scanning objects.
In pervasive computing applications, a controlled reading environment is extremely difficult to achieve, as one of the principle is to enhance existing processes "in situ", unlike the controlled conditions that can be found in industrial processes. Consider for example a logistic application, where RFID tags could be used on items inside a package in order to check for its integrity along the shipping process. Tags would likely be placed randomly on items inside the package, and reading conditions would be variable depending on where the package is checked.
RFID operation in uncontrolled environments is challenging because RFID performance is affected by multiple parameters, in particular:
- Objects materials (on which tags are attached to),
- Materials in the surrounding environment,
- RFID frequency spectrum,
- Antenna nature and placement with respect to the tags.
In controlled environment, the difficulty to read tags can be limited by using the appropriate parameters to maximize the RFID performance for the application. But in many cases, it is needed to read large number of objects of various nature, arranged randomly in a given area or container. Most pervasive computing applications fall in this context.
4.4 Data collection for precision agriculture
The use of sensor networks can be useful to support environmentally friendly production in the agricultural sector: monitoring of plant cover, plant disease detection, fine-grained plant treatments. Nevertheless, the digital tools used for this type of deployment were not designed to be broadly usable by non-specialists and have not yet established themselves among the agricultural community.
In addition, in agriculture as in many fields, the use of digital technology has mostly been carried out under the paradigm of massive data collection: logging as much information as possible, storing the data and then implementing statistical and IT methods to extract meaningful information. This approach raises problems of energy storage and consumption, increasing the environmental footprint of digital technology and limiting deployments of operational and sustainable systems.
Very small connected objects are now able to execute software codes, to drive many sensors, to send data pair with other devices in their neighborhood and to pre-process data for cleaning/aggregation. Our ambition is to optimize the crop monitoring system from a data and energy perspectives, using generic software mechanisms as close as possible to the sensor node and introducing “intelligence” into the data collection mechanisms.
Our approach is based on the quality of the data produced by the sensor nodes distributed in the environment. Data quality can be broken down into different dimensions: precision, confidence, durability, etc. Characterizing data quality requires the developer of an application to analyze and possibly control how this data is produced and collected. Usually, this task is performed on an ad hoc basis, with a strong dependence on the objectives of the data collection and not very reproducible as the environment in which the sensors are deployed evolves. The challenge is to offer mechanisms that will adapt, without additional software developments, to the many field experiments carried out for precision agriculture.
5 New software and platforms
5.1 New software
5.1.1 THEGAME
- Keyword: Contextual service
-
Scientific Description:
Context-aware applications have to sense the environment in order to adapt themselves and provide with contextual services. This is the case of Smart Homes equipped with sensors and augmented appliances. However, sensors can be numerous, heterogeneous and unreliable. Thus the data fusion is complex and requires a solid theory to handle those problems. The aim of the data fusion, in our case, is to compute small pieces of context we call context attributes. Those context attributes are diverse and could be for example the presence in a room, the number of people in a room or even that someone may be sleeping in a room. For this purpose, we developed an implementation of the belief functions theory (BFT). THE GAME (THeory of Evidence in a lanGuage Adapted for Many Embedded systems) is made of a set of C-Libraries. It provides the basics of belief functions theory, computations are optimized for an embedded environment (binary representation of sets, conditional compilation and diverse algorithmic optimizations).
THE GAME is published under apache licence (https://github.com/bpietropaoli/THEGAME/ ). It is maintained and experimented by Aurélien Richez within a sensor network platform developed by TACOMA since June 2013.
- Functional Description: THEGAME is a set of software services for detecting different types of situation in a building (presence in a room, activity level, etc.) based on a set of raw data sourced from all sorts of sensors. Written in C or Java, it can be integrated in an embedded computer: tablet, smartphone, box, etc., and can be connected to different sensor networks. It can be used to implement context-aware services: for example, to alert the user if s/he forgets to close a window when leaving the building, or to turn off the heating in an empty room, etc.
-
URL:
https://
github. com/ bpietropaoli/ THEGAME/ - Contact: Frédéric Weis
- Participants: Aurélien Richez, Bastien Pietropaoli
5.2 New platforms
5.2.1 Platform Pervasive_RFID
The RFID experiment testbed has been designed and deployed in collaboration with IETR (see Figure 2). This system allows both interactive testing as well as long running experiments of RFID reading protocols. It comprises a software platform allowing fine control over all the dynamic aspects influencing RFID readings: movements for target and antenna, RFID reader configuration, and smart antenna configuration (diversity and power control).
Keywords: Composite objects - RFID
- Participants: Paul Couderc and Alexis Girard (Univ. Rennes 1)
- Partner: Univ. Rennes 1 (IETR - lab bringing together researchers in the electronics and telecommunications)
- Contact: Paul Couderc

5.2.2 ISO/IEC 15118-2 Open source Implementation
The ISO/IEC 15118 standard, named "Road vehicles – Vehicle-to-Grid Communication Interface", defines how an electric vehicle and a charging station should communicate. It enables the Smart Charging of electric vehicles by allowing them to plan their charging sessions. As we want to be able to manage the charge of electric vehicles in our micro Smart Grid systems, we decided to implement the protocol defined by this standard. The goal is also to participate actively in the design of the new version of this protocol. During a charging session the charging station provides the vehicle with the status of the electric power grid. The vehicle is then able to plan its sharing session accordingly. It sends back its charge plan to the charging station, so that the Smart Grid is aware of it. The protocol also provides security and authentication features.
This software platform was implemented onto small PCs, and was used to control the charge in a small and portable demonstration platform, to demonstrate how it is possible to interconnect this high level decision and communication software with low level components, such as a Battery Management System (BMS), and a battery charger.
Keywords: Smart Grid - Intelligent Transport System
- Partner: IMT Atlantique
- Contact: Jean-Marie Bonnin
6 New results
—————————————
6.1 Smart City and ITS
Participants: Indra Ngurah, Christophe Couturier, Rodrigo Silva, Paul Couderc, Jean-Marie Bonnin.
The InDiD project aims at testing ITS applications on a large-scale national deployment of connected vehicles and infrastructure. It specifically targets complex use cases (so called day 1.5) and urban applications. This year, we took part in the use case specification (2.4.x tasks) and to the research activities (2.7.x tasks). We specifically contributed to the specification of the following use cases: "HD Cartography Extended services (G7)", "In-vehicle signage at a merge (G5 and G6)", "Vulnerable user at a public transport stop (I5)" and "autonomous vehicles specific use cases". On the research side, we participated in seminars and contributed to the editing of surveys about 5G communications for road (C-ITS) and cybersecurity (authentication with pseudonyms, end to end security protocols and Mobile Edge Computing specific issues).
In the Chantier 3.0 project, we continued last year's works to define a Bluetooth Low Energy (BLE) based architecture for both localization and communication with vulnerable users (workers in road and construction works). This year, we focused on the evaluation of the performance of our implementation of this protocol. We proposed an original BLE setup increasing the packet delivery ratio in the context of bidirectional periodic communications. We also worked to characterise the impact of the capture effect in BLE based communications. Beyond the Chantier 3.0, these results enable to model the performance of crowd based BLE applications such as "StopCovid".
Starting from July, we took part in the X2Rail-3 European Project on behalf of the RAILENIUM IRT (as a subcontractor). In this project we took the lead of the task 8.5 which aimed at writing a Protection Profile for the "Adaptable Communication Systems (ACS) Components". ACS is the new generation of communication systems for railways. It enables unified IP based train to ground communications where data is dynamically routed over heterogeneous Radio Access Networks or several providers. Our contribution was related to the architecture definition on the one hand and on the cybersecurity requirements (Protection Profile) on the other hand.
6.2 Strengthen confidence in users' positions
Participants: Yoann Maurel, Paul Couderc.
Confidence in location is increasingly important in many applications, in particular for crowd-sensing systems integrating user contributed data/reports, and in augmented reality games. In this context, some users can have an interest in lying about their location, and this assumption has been ignored in several widely used geolocation systems because usually, location is provided by the user’s device to enhance the user’s experience. Two well known examples of applications vulnerable to location cheating are Pokemon Go and Waze.
Unfortunately, location reporting methods implemented in existing services are weakly protected: it is often possible to lie in simple cases or to emit signals that deceive the more cautious systems. For example, we have experimented with simple and successful replay attacks against Google Location using this approach (see Figure 3).
An interesting idea consists in requiring user devices to prove their location, by forcing a secure interaction with a local resource. This idea has been proposed by several works in the literature; unfortunately, this approach requires ad hoc deployment of specific devices in locations that are to be "provable".
Last year we proposed an alternative solution using passive monitoring of Wi-Fi traffic from existing routers. The principle is to collect beacon timestamp observations (from routers) and other attributes to build a knowledge that requires frequent updates to remains valid, and to use statistical test to validate further observations sent by users. Typically, older data collected by a potential attacker will allow him to guess the current state of the older location for a limited timeframe, while the location validation server will get updates allowing him to determine a probability of cheating request. The main strength is its ability to work on existing Wi- Fi infrastructures, without specific hardware. Although it does not offer absolute proof, it makes attacks much more challenging and is simple to implement.
We are now exploring a broader approach, considering other radio signals in order to have a diversity of sources from which to pick the features used to generate the location proof. We also consider the attack side, which presents interesting perspectives regarding the actual strength of existing services and the potential protection improvements that our approach can provide. A student has just started in internship on this topic.
6.3 Local energy usage optimisation: A Digital Twin for microgrid case study
Participants: Alexandre Rio, Yoann Maurel.
This work is part of projects aimed at optimizing the use of renewable energies. It is carried out in collaboration with the Diverse team and the company OKWind specialized in the production of solar panels.
Renewable energies currently benefit from numerous subsidies to encourage their use and thus reduce greenhouse gas emissions. We believe that renewable energies can be profitable on their own without the need for these subsidies. Energy management is also a major economic concern for industrials and microgrids in general. A number of technological means are available to operators in order to regain some control over their consumption. They may install local renewable energy sources, energy storage or they can act on their consumption to better match the production, that is Demand Response.
So-called clean energies cannot be used efficiently to replace fossil fuels without a great amount of adaptation. Indeed, during peak periods, the electricity produced is competitive, but too often the expected consumption is not adapted to the production. Consequently, achieving a profitable self-generation system is in practice a matter of trade-off involving several factors: the scale of the energy sources, the size of the batteries used, the desired level of autonomy, environmental concerns and the organization of demand.
Although much work has been done in the literature on the effects of the various factors, there are few approaches that provide a complete model. Multiple methods have emerged to evaluated the interest of various configuration though simulation. These tools are mostly specific to a particular type of energy source and require knowledge in numerical computing.
Our objective is to provide a methodological framework that encompasses the diversity of knowledge, production and consumption tools, agricultural activities and predictive algorithms.
In the first two years of this thesis, we argued that model-driven engineering is suitable for the development of such a model, and we presented a first implementation. We defend a methodology for experts in the energy sector based around the Digital Twin. We propose a Digital Twin to simulate the behavior of a microgrid, evaluate the impact of hardware or habits changes and to act on real devices. Our approach aims to be modular to address the heterogeniety of the real world, extensible to follow the industrial sites evolution and accessible to experts though a Domain Specific Language.
This year was spent consolidating results with industrial companies. We focused particularly on the agricultural world. OKWind benefits from a very large implantation which allowed us to implement the approach on different test sites. The prototype consolidated as a platform proved to be robust enough to be adopted by the company for the conduction of new projects and is now part of the range of tools available to the company for real agricultural site instrumentation.
This work has led to two publications and a thesis that will be defended this february.
6.4 Wireless sensors for precision agriculture
Participants: Jean-Marie Bonnin, Frédéric Weis.
This work is carried out within the framework of a collaboration between the Inria-EASE team, and the Demecology (Dynamics-Evolution-Modeling-Ecology) team of INRAe, which carries out work in plant epidemiology. The objective is to develop precision monitoring solutions for their experimental vegetal plots.
Our ambition is to optimize the crop monitoring system using generic software mechanisms implemented as close as possible to the sensor nodes and introducing “intelligence” into the data collection mechanisms. Our approach is based on the quality of the data produced by the sensor nodes distributed in the environment. However, current frameworks for managing the nodes and exchanging data do not provide data quality (DQ) metrics. Applications deployed for precision agriculture need to know how "good" the data are for use. Actually, specifying/expressing DQ requirements is a subjective task, depending on the specific needs of each targeted application.
We focus on system and network level mechanisms allowing an application to act in the environment (i.e., on the network infrastructure and / or on directly connected objects) to adapt the data collection, according to an expected level of quality. The software mechanisms studied have to be compared to the experimental models developed by the INRAe Demecology team in different fields: monitoring of the plant cover, detection of the conditions of appearance of diseases, etc.
This year, our efforts were focused on designing and developing a software and hardware platform intended to provide tools for the EASE team network experiments, but also to supply a wireless measurement station answering to the INRAE’s laboratory needs concerning their studies on plant pathology. Therefore, our system must be able to transmit physical data to a remote server/network. For this purpose, the LoRaWan network has been chosen for its long range capabilities. The station also uses the 802.15.4 protocol (2.4GHz, short to medium range) in order to create a mesh network to cover wider measurement surfaces.
In this context, a state of the art has been established on low energy MCU based systems and their uses within the embedded systems associated with the operating system developed by INRIA: RIOT. Some technical aspects are crucial in order to obtain an efficient platform:
- The energy management;
- a versatile, reliable and straight forward network configuration;
- an easily usable and deployable software layer.
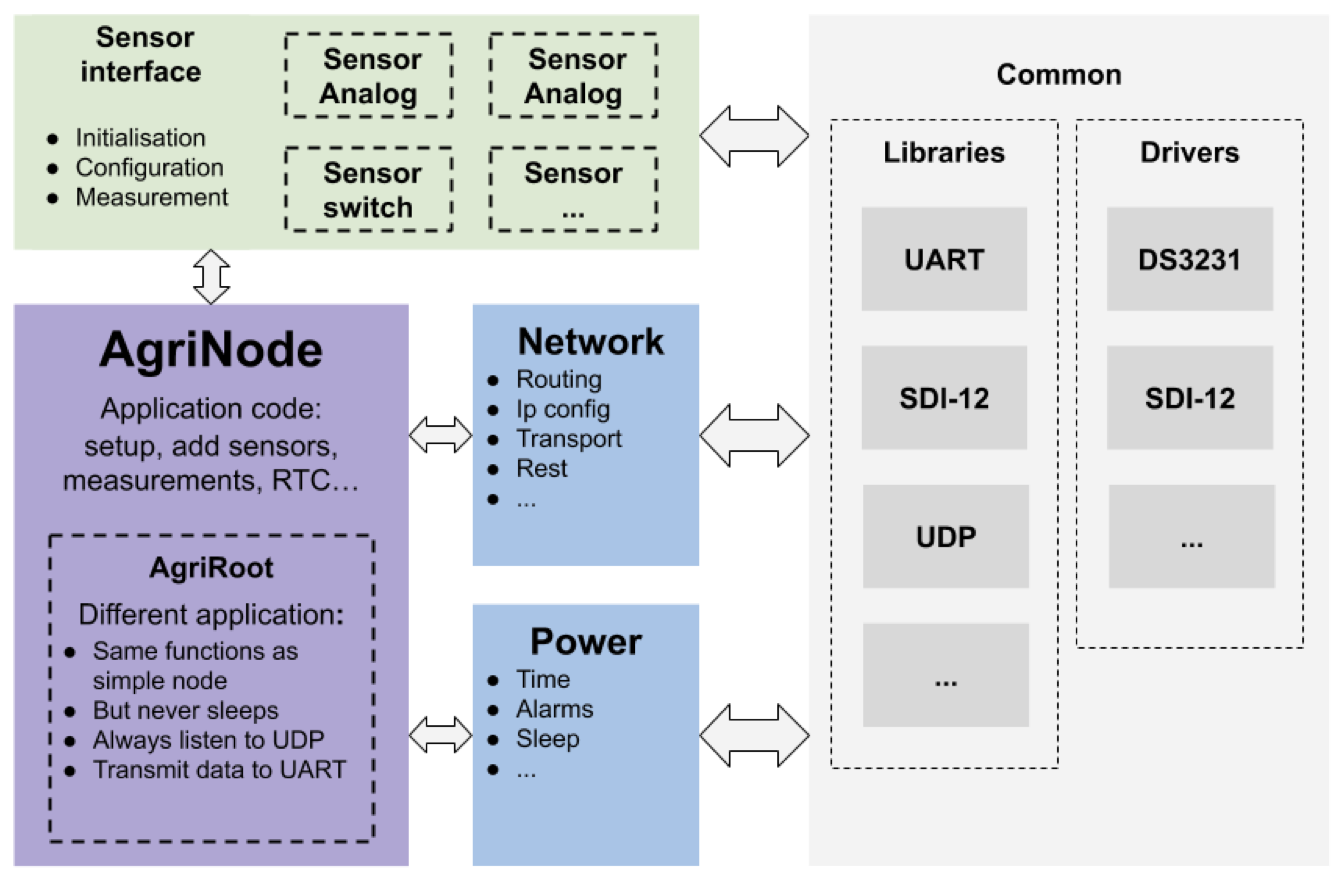
The system’s software uses the tools provided by RIOT OS. An additional abstraction layer has been developed to ease the platform use and its future developments.
As illustrated in Figure 4, the different software parts which have been developed and are currently available. A set of libraries and drivers (defined above as “Common”) allows to integrate the protocols used by INRAE’s sensors as well as the hardware used by the platform itself. A sensor interface is used to provide an abstraction layer between the application and the lower layers (communication protocols) of the software. This makes the installation and removal of sensors on the platform easy. The “network” and “power” APIs respectively supply network and power management functionalities for the application. It is worth noting that, as with the hardware aspect, special attention has been paid to the energy management on the software level. This has been archieved by exploiting the various mechanisms provided by RIOT.
Today, the first experiments at the INRAE have been completed. These tests were mainly realized to evaluate the platform’s capabilities concerning network reliability, battery life, and the range of the different communication protocols. The results on this last element were good and better than expected whether using LoRaWan or the 802.15.4 protocol. The battery life was satisfactory since a small 1000 mAh battery was enough to power the system for a month. Some instabilities were noticed with the 802.15.4 mesh network when increasing the number of nodes. This last point is currently being studied.
7 Bilateral contracts and grants with industry
7.1 Bilateral contracts with industry
- Project: SIMHet
- Partner: YoGoKo
- Coordinator: JM. Bonnin
- Starting: Nov 2015 - Ending: April 2020
- Abstract: The SIMHet project is performed in partnership with YoGoKo, a start-up that develops innovative communication solutions for cooperative intelligent transport systems. The SIMHet project aims to develop a decision making mechanism that would be integrated in the ISO/ETSI ITS communication architecture. It will allow mobile devices or mobile routers to choose the best network interface for each embedded application/flow. For example, in a vehicular environment this mechanism could manage global (Internet) and local connections for each on board device/application, in order to ensure that applications and services are always best connected. Being aware that "best" concept is context-dependent, such a decision making mechanism should take into account requirements from different actors (e.g., applications, user, network administrators) and contextual information. One of the difficulties is to take advantage of the knowledge the system could have about near future connectivity. In the vehicular context such information about the movement and the availability of network resources is available. If taking into account the future makes the decision making more complex, this could allow a better usage of network resources when they are available. Since current solutions in the market are based on very simple decisions (use WiFi if available and 3G elsewhere), this smart mechanism will give a competitive advantage for YoGoKo over its competitors.
- Project: Agri-BIoT
- Partners: Inria - IMT-A
- Coordinator: JM. Bonnin
-
Abstract: A startup project (Agri-BIoT) involving Inria and IMT Atlantique people is getting ready with edge computing solutions targeting agriculture applications. A core component of the solution is an RFID based local storage infrastructure for in situ annotations and data tracking.
The team is contributing to this project with his experience in developing RFID based distributed storage and operating RFID in adverses conditions. The RFID component of Agri-BIoT requires an extensive evaluation of the performance of UHF RFID tags in the farming context, which was largely unknown, and benchmarking existing hardware on the market. The facility developed in the Pervasive_RFID provided an excellent tool for testing and qualifying the RFID equipment to be used in Agri-BIoT, which was the purpose of the Tagri project (see section 1).
The projet has been selected and founded in the Inria Startup Studio.
More information about Agri-BIoT is available on the startup website: https://
agribiot. fr/ en/ index. html.
7.2 Bilateral grants with industry
- OKWIND
- Coordinator: Y. Maurel
- Starting: April 2017 - Ending: April 2020
- Abstract: OKWind 1 is a company specialized in local production of renewable energy. This project, with Inria DiverSE and EASE teams, aims at building a system that optimizes the use of different sources of renewable energy, choosing the most suitable source for the current demand and anticipating future needs, so as to favor the consumption of locally produced electricity. The system must be able to model clients' activities. It must also trigger actions (local consumption vs. local storage). The final goal is to use "locally produced" energy in a smarter way and to tend towards a self-consumption optimum. This contract funds Alexandre Rio's PhD grant.
8 Partnerships and cooperations
8.1 European initiatives
8.1.1 Collaborations in European programs, except FP7 and H2020
- X2Rail-3
- Coordinator: C. Couturier
- Starting: mid 2019; Ending: Dec 2023
- Partners: Thales, Alstom, Hitachi Rail STS, AZD, Bombardier, CAF, CEIT, Deutche Bahn, DLR, HaCon, Indra, Kontron, Mermec, NetworkRail, Railenium, SNCF Réseau, Trafikverkert, Siemens
-
Abstract: This European project aims to continue the research and development of key technologies to foster innovations in the field of railway signalling, telecommunication, testing methodologies and Cyber Security, as part of a longer term Shift2Rail IP2 strategy towards a flexible, real-time, intelligent traffic control management and decision support system.
The actions to be undertaken in the scope of X2Rail-3 are related to the following specific objectives:
- To improve line capacity and to achieve a significant reduction of the use of traditional train detection systems by means of the introduction of the Moving Block together with train positioning;
- To overcome the limitations of the existing communication system by adapting radio communication systems which establish the backbone for the next generation advanced rail automation systems;
- To ensure security among all connected signalling and control systems by developing new cyber security systems dedicated to railways;
- To analyse new signalling concepts (Virtual Coupling) that potentially would be able to improve line capacity, reduce LCC and enhance system reliability.
- To improve standardization and integration of the testing methodologies reducing time to market and improving effectiveness in the introduction of new signalling and supervision systems;
- To ensure the evolution and backward compatibility of ERTMS/ETCS technologies, notwithstanding of the required functional enrichment of the future signalling and control systems.
In this project, we act on behalf of the RAILENIUM IRT (as a sub-contractor). Discussions are ongoing with RAILENIUM in order to reinforce the cooperation between them and IRISA/Inria.
8.2 National initiatives
- InDiD
- Coordinator: JM. Bonnin
- Starting: mid 2019; Ending: Dec 2023
- Partners: 20+ French partners including cities (Paris, Grenoble...), road operators, transport operators, academics (incl. IMT Atlantique) and industrials
- Abstract: InDiD is one of 13 French projects out of 148 European projects selected by the European Commission within the framework of the last Connecting Europe Facility (CEF) call for proposals. The project benefits from a co-funding rate of 50% on behalf of the European Union. It follows the Smart Cooperative Transport Systems projects SCOOP@F, C-ROADS France and InterCor. The project aims at expanding the coverage of use cases deployed in previous projects (emergency braking, accident, work...) and develop new use cases dealing with urban area, but also use cases of increased perception for autonomous vehicle. In addition, it deals with high definition digital mapping of the infrastructure. Connectivity along with mapping shape the digital infrastructure of tomorrow, an essential addition to the physical infrastructure. InDiD aims at continuing the deployment of Cooperatives Intelligent Transport Systems on new road experimentation sites in order to expand the services coverage offered by the infrastructure. Pilot sites are located on 4 main French geographic areas, on the Mediterranean side, in the south-west area, at the centre and in the north of France.
- TAGRI
- Coordinator: P. Couderc
- Starting: Nov 2019; Ending: Nov 2020
-
Abstract: Tagri is a 12 months innovation action supported by a CominLabs grant, started on 2019-11-01 and ended on 2020/10/31. It follows up the previous PervasiveRFID project, a joint INRIA – IETR collaboration. Tagri aims at developing an operational UHF RFID solution for agricultural applications where tags are used as a pervasive storage to track important data related to the production. Tagri is using the RFID research facility from Pervasive_RFID project to study the behavior and performance level of UHF RFID in the context of agricultural applications, which is new as the standard RFID technology used in farming is LF based.
Historically, LF was selected because it was reliable for bio-tags attached to animal, and the driver application for RFID in smart farming was breeding. The first application field considered is wineries, in collaboration with the AgriBiot start up project. A preliminary field survey allowed us to collect the relevant information to design a benchmark for RFID operations in this context. A set of potentially adverse elements were identified in the vineyard such as:
- Soil thickness (for buried tags or tags attached to a buried support)
- Wood thickness (for tags attached to wooden pole)
- Metal presence
- Humidity, or wet conditions
- Copper based fungicide
The necessary hardware and materials were acquired to reproduce the vineyard situations on the Pervasive_RFID experiment platform. Despite some limitations of in the experiments, the Tagri results have shown that for most situations, except tags buried in wet soil, we are not in marginal performance conditions for UHF RFID tags and they should be readable with the adequate readers. Several tags on the market provide adequate performance for the vineyard application target by Agri-BIoT, and we found that the most sensitive tags (longest range) are not the best for a good overall performance in wide variety of conditions.
8.3 Regional initiatives
- Chantier 3.0
- Coordinator: JM. Bonnin
- Starting: Jan 2019; Ending : Dec 2021
- Partners: Agemos, YoGoKo, IMT Atlantique
-
Abstract: Co-founded by "Région Bretagne" Chantier 3.0 is a "PME Project" aiming at increasing safety of workers in construction sites and road works. In these scenarios, vehicles represent a danger for the workers. Knowing the position of the vehicles and workers, it is possible to alert workers who are located in a safety perimeter around the vehicles. The project addresses the challenges of 1) precise localisation with low or medium cost wearable devices and 2) of dynamically setting up a reliable communication network in harsh environments mixing indoor and outdoor conditions.
The key technologies used to solve theses issues include: fusion of localisation data (GPS, acceleration integration, location anchors, angle of arrival and time of flight of radio signals), opportunistic short range broadcast communications, ITS communication protocols and system integration. EASE brings it expertise in all of theses domains in order to enhance the reliability of the system, to make it affordable and to pave the way for its standardisation.
9 Dissemination
9.1 Promoting scientific activities
9.1.1 Scientific events: selection
Member of the conference program committees
- PC member of eHPWAS 2020, AdHoc Now 2020, F. Weis
- PC member of ISCC 2020, C. Couturier
- PC Member at Vehits’20, Vehits’21, PIMRC’20, ARCI’21, 3ICT’2020, J.-M. Bonnin
Reviewer
- “IEEE Intelligent Transportation Systems Magazine”, “JCRAI 2020 Conference”, “Annals of Telecommunications”, “The Computer Journal”, J.-M. Bonnin
9.1.2 Invited talks
- "Véhicules connectés et coopératifs", organized by "Carnauto" and "Pôle Véhicule du Futur", november 3rd, C. Couturier
- “Localized Interactions for an Open Urban ITS Ecosystem”, JFLI Workshop on Next Generation Networking, Tokyo, February 17, J.-M. Bonnin
- "Véhicules connectés et coopératifs", organized by "Carnauto" and "Pôle Véhicule du Futur", november 3rd, J.-M. Bonnin
- “Systèmes de Transport Intelligents Coopératifs dans un Environnement Urbain”, CSTI’20 (1er colloque francophone des systèmes de transports intelligents, Tunis, November 11, J.-M. Bonnin
- “Garantir Anonymat et Sécurité dans les ITS Coopératifs”, Rendez-vous Carnot, November 19, J.-M. Bonnin
- “Secure Local Cooperations: the Case of Urban ITS”, SophI.A Summit, November 19, J.-M. Bonnin
9.1.3 Leadership within the scientific community
9.1.4 Scientific expertise
- Head of the scientific committee of InOut2020, J.-M.Bonnin
- Member of the scientific council of the Id4Car cluster, J.-M. Bonnin
- Scientific advisor of the YoGoKo startup, J.-M. Bonnin
- Co-head of "the pole Digital Society of the MSHB" (Maison des Sciences de l’Homme de Bretagne), J.-M. Bonnin
- Project evaluation for ANR, Belgium, Id4Car, Région Pays de la Loire, Région Grand Est, J.-M. Bonnin
- Expert for CSV board of "Pôle Images et Réseaux", projects reviewing and selection, strategic roadmap definition, P. Couderc
9.1.5 Research administration
- Member for the IRISA Laboratory Council, JM. Bonnin
- Member of the scientific council of ECAM (Engineering school), JM. Bonnin
9.2 Teaching - Supervision - Juries
- Master 2 SmartMobility: Communications for ITS, J.-M. Bonnin, Telecom Paris and ENPC
- Master 2 IoT: SmartCity, J.-M. Bonnin, IMT Atlantique Continuous training: Communications for Autonomous and Cooperative vehicle, Communications for ITS, J.-M. Bonnin, IMT Atlantique
- Master 2 : Autonomous vehicles and cooperation, J.-M. Bonnin, ENSSAT
9.2.1 Teaching
- L2/L3: network computing (lectures, tutorials, labs), 250 hours, F. Weis, Univ. Rennes 1
- Master 2: Wireless LANs, F. Weis, 30 hours, M2, IMT Atlantique
- Master 2: Pervasive computing and IoT system architectures, 4 hours, P. Couderc, Univ. Rennes 1
- Master 1: Network programming (lectures, tutorial, labs), 78 hours, Y. Maurel, Univ. Rennes 1
- L3/M2: network communications protocol for building automation (lectures, labs), 80 hours, Y. Maurel
- Master 2: Software engineering (lectures, tutorial, labs), 82 hours, Y. Maurel
- Master 2 : Mobility management in the Internet, JM. Bonnin, IMT Atlantique
- Master 2 Smart Mobility : Communications for ITS, JM. Bonnin, IMT Atlantique
- Master 2 IoT: Smart City, JM. Bonnin, ENSI Tunis
- Continuous training: Communications for Autonomous and Cooperative vehicle, Communications for ITS, JM. Bonnin, IMT Atlantique
- Master 1: Network programming (lab and project), 72 hours, C. Couturier, IMT Atlantique
- Master 1: IP networks (lectures, tutorial), 24 hours, C. Couturier, IMT Atlantique
- Master 2: Enterprise Network Design, 12 hours, C. Couturier, IMT Atlantique
- Master 2: Bid to Call for Tender, 12 hours, C. Couturier, IMT Atlantique
- Master 2: Supervision of the Networking and Telecom curriculum of FIP3A, C. Couturier, IMT Atlantique
- Master 2: Tools for cloud computing , 18 hours, C. Couturier, IMT Atlantique
9.2.2 Supervision
- PhD in progress: Indra Ngurah, Car-based Data Collection for Low Energy Devices (Car-based DC4LED), May 2016, Jean-Marie Bonnin
- PhD in progress: Alexandre Rio, "Modélisation des activités de site consommateur d'énergie", Octobre 2016, Olivier Barais (UR1) and Yoann Maurel
- PhD Rodrigo Silva, "Mécanisme de décision multi-critères pour le placement de flux en environnement hétérogène et changeant", Nov. 2015, Jean-Marie Bonnin, defense in January 2020
9.2.3 Juries
- PhD defense: Justin Lev, “A study of 3D point cloud features for shape retrieval”, May 11, J.-M. Bonnin, president
- PhD defense: Safa Mejri, “Contrôle de congestion dans les réseaux orientés contenu”, October 7, J.-M. Bonnin, referee
- PhD defense: Dina Tarek, “Développement du Protocole de Partage du Spectre pour la Radio Cognitive Internet des Objets”, December 18, J.-M. Bonnin, president
9.3 Popularization
9.3.1 Education
- “Towards Cooperative Urban ITS”, in EIT Digital Summer School, July 9, J.-M. Bonnin
9.3.2 Interventions
- “Quelles infrastructures de communication pour les ITS coopératifs ?” in ATEC ITS France after work “Architecture des réseaux : quels apports pour la mobilité ?”, May 26, J.-M. Bonnin
10 Scientific production
10.1 Major publications
- 1 inproceedings EraRFID: Reliable RFID systems using erasure coding. IEEE International Conference on RFID 2015 San Diego, United States IEEE April 2015
- 2 inproceedingsLocation corroboration using passive observations of IEEE 802.11 Access PointsCCNC 2019 - 16th IEEE Consumer Communications & Networking ConferenceLas Vegas, United StatesIEEEJanuary 2019, 1-7
- 3 incollectionOpportunistic Networking for ITSITS 2016 : Intelligent Transport Systems: Past, Present and Future DirectionsNova publisher2017, 59 - 86
10.2 Publications of the year
Doctoral dissertations and habilitation theses
