2023Activity reportProject-TeamFUN
RNSR: 201221009N- Research center Inria Centre at the University of Lille
- Team name: self-organizing Future Ubiquitous Network
- Domain:Networks, Systems and Services, Distributed Computing
- Theme:Networks and Telecommunications
Keywords
Computer Science and Digital Science
- A1.2.1. Dynamic reconfiguration
- A1.2.3. Routing
- A1.2.5. Internet of things
- A1.2.6. Sensor networks
- A1.2.8. Network security
- A1.4. Ubiquitous Systems
- A1.6. Green Computing
- A5.10.6. Swarm robotics
Other Research Topics and Application Domains
- B3.5. Agronomy
- B3.6. Ecology
- B5.1. Factory of the future
- B5.9. Industrial maintenance
- B6.4. Internet of things
- B7.2.2. Smart road
- B8.1. Smart building/home
- B8.1.2. Sensor networks for smart buildings
- B8.2. Connected city
1 Team members, visitors, external collaborators
Research Scientists
- Nathalie Mitton [Team leader, INRIA, Senior Researcher, HDR]
- Valeria Loscri [INRIA, Researcher, HDR]
Post-Doctoral Fellows
- Adriana Arteaga Arce [INRIA, Post-Doctoral Fellow]
- Carol Habib [INRIA, from Oct 2023]
- Nassima Merabtine [INRIA, Post-Doctoral Fellow, until Feb 2023]
- Aya Moheddine [INRIA, Post-Doctoral Fellow, from Jul 2023]
- Damien Wohwe Sambo [INRIA, Post-Doctoral Fellow]
- Selma Yahia [INRIA, Post-Doctoral Fellow, from Aug 2023]
PhD Students
- Ildi Alla [INRIA]
- Aymen Salah Eddine Bouferroum [INRIA, from Oct 2023]
- Hazem Chaabi [INRIA]
- Selina Cheggour [UNIV LILLE]
- Jana Koteich [INRIA]
- Nina Santi [INRIA]
- Marwa Slimene [INRIA, from Jun 2023]
- Jiali Xu [INRIA, from Mar 2023]
Technical Staff
- Lucille Colin [INRIA, from Sep 2023, Project Manager]
- Solenne Fortun [INRIA, Project Manager]
- Etienne Profit [INRIA, Engineer]
- Prakriti Saxena [INRIA, Engineer, until Aug 2023]
Interns and Apprentices
- Simon Lacan [INRIA, Intern, from May 2023 until Aug 2023]
- Tom Mathieu Ruckstuhl [UNIV LILLE, Intern, from May 2023 until Jun 2023]
Administrative Assistant
- Anne Rejl [INRIA]
Visiting Scientists
- Gerardo Hernandez Oregon [Instituto Politécnico Nacional de Mexico, from Feb 2023 until Jul 2023, Visiting PhD student]
- Herve Olou Babatounde [University of Benin, from May 2023 until Jul 2023, Visiting PhD student]
2 Overall objectives
With the foreseen increase of communicating devices around the world, many challenges will arise. Among them, the most predominant ones are certainly the scarcity of the medium, the energy consumption, the lack of interoperability and the security of these devices and their data.
Our objectives are to address these different challenges for the self-organization of these Future Ubiquitous Networks. Our focus will be set on wireless heterogeneous communicating objets that feature different limitations and constraints such as hardware limitations (low computing and memory storage capacities), limited energy, potentially high mobility or hostile environment. By wireless, we mean any communication with no wire. Objects could thus communicate through traditional RF transmissions or any alternative way such as visible light communication (VLC) or molecular technologies. They can be heterogeneous in terms of hardware processing, mobility patterns (mobility can be undergone or controlled, unknown or predictable), communication technologies, etc. For all these families of devices, we will design holistic communication protocols to allow them to efficiently function and cooperate in a harmonious energy- and data-priority aware fashion. These protocols will focus on low communication layers (PHY, MAC and NET) and combine opportunistically heterogeneous device features to make a global efficient behavior emerge.
The goal of the FUN project team is to leverage the heterogeneity of the new communicating devices to override major rising issues. Heterogeneity and mobility will be seen as opportunities and strengths rather than flaws and exploited. Our protocols will foster the cooperation between devices in a secure, energy efficient and frugal way.
3 Research program
Objectives and methodology
To achieve our main objectives, we will mainly apply the methodology depicted in Figure 1 combining both theoretical analysis and experimental validation. Mathematical tools will allow us to properly dimension a problem, formally define its limitations and needs to provide suitable protocols in response. Then, they will allow us to qualify the outcome solutions before we validate and stress them in real scenarios with regards to applications requirements. For this, we will realize proofs-of-concept with real scenarios and real devices. Differences between results and expectations will be analyzed in return in order to well understand them and integrate them by design for a better protocol self-adaptation capability.
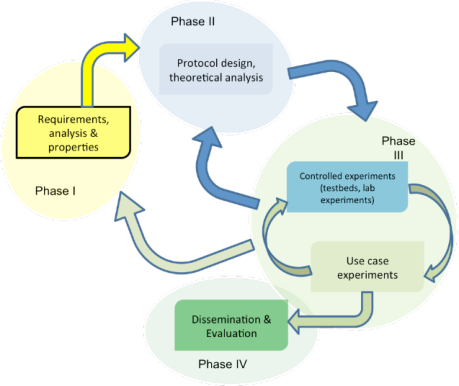
Methodology to be applied in FUN.
3.1 Research axes
To reach this overall objective, we will develop our research around the three following axes: i) Frugality and opportunism, ii) Security and iii) Interconnectivity. Note that these axes are not completely independent nor hermetic. A transversal axis will be the deployment and set up of experimental testbeds.
3.1.1 Frugality and opportunism
As the objects we consider are resource-limited and that they use a rare resource to communicate (wireless medium), all our solutions must be frugal and use as little resources as possible. A way to alleviate the energy consumption and the medium utilization is to reduce the data to send and/or to smartly decide when to send it, by what mean and to whom without jeopardizing the accuracy and completeness of the data. When to send a data can indeed impact the resource utilization since in a dynamic environment, some interference could appear at different times; in a mobile environment, a data could be carried rather than transmitted; in an energy-harvesting network, the amount of available energy could grow. We thus intend to closely analyse and understand interference impacts on different environments and contexts on one hand (as the research initiated in LumiCar, EthiCam, AgriNET) and to exploit them in the design of our protocols.
Deciding what data to send allows for a data reduction and resource savings. To do so, we will use machine learning techniques (e.g. Thompson sampling, Bayesian approaches, linear approaches, ARMA, Pearson sampling etc) that we will adapt to fit the specific context of the applications. The idea is to propose predictive algorithms to "guess" a data rather than transmitting it. This is among others what we are investigating in the AgriNET project.
In case of the availability of multiple communication technologies, the choice of this technology will impact the global system since all technologies do not provide the same QoS performances (delays, throughputs, etc) with different energy consumptions and do not face interferences the same way depending on the environment. We will thus analyse and understand all these specificities to combine them to get the best performances.
In all above mentioned cases, we will try to provide time and space depend protocols as frugal as possible but still meeting the application requirements and expectations. This will be done by opportunistically leveraging network particularities (multiple technologies, mobility, energy-harvesting, etc) based on experimental-driven behavioral analysis, as initiated with the collaboration with Sencrop.
3.1.2 Security
Security of wireless transmissions is a rising issue that gains importance with the increase of wireless devices. Our team has just started research work in security but we will pursue our efforts. Our goal will be to secure the wireless communications in different ways. Indeed, traditional security techniques (cryptography, firewalls, etc) cannot be applied in FUN because of their pervasive feature and limited resources. In terms of Security, we will focus on the lowest layers of the communication stack in order to first identify attacks that may appear at these levels and proposes i) recovering and healing solutions and ii) new solutions that are robust by design.
At the MAC layer, we will for instance investigate denial of sleep-like attacks that aim to make nodes deplete their energy quickly. At NET layer, we will investigate different routing protocols that are able to detect an abnormal behavior of a neighbor node to then exclude it from any network operation. This has obviously to be done locally and in a distributed way. In all cases, the same methodology will be apply: observe, understand and model, to then identify the threat or the malicious entity and finally heal. In some case, we can leverage the characteristics of the communication technology to reinforce the security aspect, such as VLC that may allow Line-of-Sight (LOS) communications and for which certain types of attacks that can be effective for "traditional" wireless systems (i.e., jamming attacks) cannot be easily applied. The works initiated in the framework of the H2020 CyberSANE project, in the DGA grant and in DEPOSIA project, fall within this perspective.
3.1.3 Interconnectivity
Another challenge faced by FUN is their interconnectivity to traditional networks such as Internet and the data offloading. Because of their limited capacity, FUN devices may need to call for remote services. These latter are usually hosted in the cloud. But being served by the cloud implies sometimes long latency and uselessly congest the wired network. We will thus investigate how to get these services closer to the FUN devices to alleviate the energy consumption, reduce latency and network congestion. This will go from edge and mobile edge deployments to service distribution over more powerful heterogeneous devices. Our research will analyse devices needs and estimate in time and space the services to be deployed. When the service is expected to be temporary, mobile edge services could be deployed and so our investigations will include the self-deployment techniques. When some already deployed wireless devices feature more capacity, we can leverage this node heterogeneity to distribute the services over these nodes. The research conducted towards this third objective will call for adaptation of machine learning techniques to predict needs, to mobility modeling and cross-layer communication protocols. This has been initiated in the DRUID-NET project.
4 Application domains
The FUN research can be applied in various applications. We only cite here the ones on which we currently focus.
- Smart Agriculture: Wireless sensors are more and more deployed in remote fields and livestock for an accurate monitoring. This generates new challenges in terms of reliability, energy consumption and range as investigated in the D4SC and Agrinet projects.
- Vehicular networks: vehicles become smarter and smarter, providing new useful services. But communications between vehicles on one hand and between vehicles and road infrastructures on the other hand raise a lot of challenges as investigated in the CONCESE project.
- Smart infrastructures: FUN research can also apply to different urban and civil infrastructure like road monitoring (as in the DEFI with CEREMA) or Smart Grids.
- Logistic and traceability: RFID and IoT are the key technologies to enable large scale traceability. They are for instance investigated in the GoodFloow project.
- Post disaster recovery: New services of different kinds (communications, processing, context analysis) need to be deployed quickly and efficiently after a disaster in order to support rescue operations. This requires adaptable and flexible resource deployment such as investigated in NEPHELE and DRUID-NET projects.
5 Social and environmental responsibility
In all our research, we really care to the low energy consumption by design but also to the final goal, paying a special attention to applications that support environement, decarbonisation or social concerns. This is reflected by the main topic of most of our collaborative projects.
6 Highlights of the year
European Commission's Innovation Radar identified Inria FUN in the project as one of the 3 'Key Innovators' in the development of the Integrated incident handling and response for critical infrastructure in the CyberSane project.
7 New software, platforms, open data
We believe open software and open data collection or generation tools are mandatory in our research, to ensure reproducibility and repeatability. Therefore we have built two main software tools. The first one relies on the FIT IoT LAB open testbed and allows for the generation of network data. The second one allows for the collection of real communication traces. Both our tools are made available on open gitlab and the dataset either generated or collected are freely shared. The software tools call to the enrichment of these datasets.
7.1 Open data
Sisyphe
Participants: Nathalie Mitton [contact person], Nina Santi.
The Sisyphe tool 29 relies on the FIT IoT-Lab large scale testbed and state-of-the-art software engineering techniques to produce, collect and share artifacts and datasets in an automated way. This makes easy to track the impact of software updates or changes in the radio environment both on a small scale, e.g. during a single day, and on a large scale, e.g. during several weeks. By providing both the source code for the trace generation as well as the resulting datasets, we hope to reduce the learning curve to develop such applications and encourage reusability as well as pave the way for the replication of our results. While we focus in this work on IoT networks, we believe such an approach could be used in many other networking domains.
All generated dataset and open software are available here and in Zenodo. It has been then extended to include mobility in data generation. This extension is available here.
PILOT
Participants: Jana Koteich, Nathalie Mitton [contact person].
PILOT 28 dataset is a Privacy-preserving data collectIon tool of wireLess cOmmunication Technologies. The collected dataset is a collection of four jointly collected information in different mobility contexts. It includes three wireless communication technologies: WiFi probe-responses, BLE (Bluetooth Low Energy) beacons, and LoRa (Long Range Radio) packets, plus additional information: Acceleration, Roll, and Pitch, all collected at the same time. We provide the keys to reproduce such data collection and share the datasets already collected. The dataset is collected for approximately 90 hours, with a size of 200 MB using FiPy devices from Pycom and it is uploaded to GitHub. The dataset's utility is validated through the application of a classification machine learning model 24 that determines the real-life situation of devices through the communication links monitored in different scenarios with an accuracy of 94%. Thus, we believe that such dataset is important for human mobility studies and applications of integrated sensing systems since it offers a new form of a classified collected data that does not exist in the already published datasets.
All collected dataset and open software are available here.
8 New results
8.1 Security
Participants: Valeria Loscri, Selma Yahia, Nassima Merabtine, Ildi Alda, Jiali Xu, Aya Moheddine, Aymen Bouferroum, Nathalie Mitton.
Wireless networks have enabled the development of new communication paradigms, including cellular networks and the Internet of Things (IoT). Due to the openness of the wireless medium, these new paradigms present new challenges in terms of resource allocation, interference management, and novel attack strategies. To deal with these challenges, several wireless communication protocols envision the use of different frequency bands for communications, and each frequency band is separated into channels. Exploiting this paradigm, channel hopping has been proposed to regularly or adaptively change the communication channel assigned to nodes in the network to limit both collisions and interference generated by neighboring devices. Several standard network protocols use channel hopping methods, with examples such as 802.15.4 protocol with the Time Slotted Channel Hopping (TSCH) or Bluetooth with the Frequency Hopping Spread Spectrum (FHSS) and Adaptive Frequency Hopping Spread Spectrum (AFH). Channel Hopping schemes are also developed in cognitive radio to limit the noise effects and improve the channel saturation problem. Channel hopping is also widely applied in drones technology and it is normally employed to mitigate the physical attacks (e.g., jamming attacks). In 21, we consider a smart jamming attack, without needing of previous knowledge on the victim's behavior. The main objective is to learn the victim's channel hopping strategy form real-time channel measurements. The validation is based on real experiments on a testbed created from scratch in our laboratory. The evaluation is comparing different appraoches, such as random channel hopping, incremental channel hopping, and show the superiority of our smart approach in terms of effectiveness, response time and accuracy. We are also extending this approach to drones systems, by considering DJI nodes, implementing ad-hoc channel hopping methods. Of course, the channel hopping method is prone to specific attacks, and if a malicious node has the willingness to hinder a correct communication between a transmiutter and a receiver, it can exploit it to create Denial Of Service (DoS) attacks. For these reasons, it is paramount that the channel selection is based on advanced methods. In 14 we propose a channel selection model able to assist wireless nodes in choosing the best channel to transmit on, that is suitable for wireless devices and does not require standard modifications. The proposed model, developed for wireless technologies based on the association phase, can be implemented in several wireless technologies, spanning from IEEE 802.15.4 to Z-Wave, just to cite a few. We were inspired by the concept of trustworthiness and took advantage of the well-known trust management techniques. In this scenario, the communication between nodes involves two different roles: the first represents the trustor, and it has to trust the other one, which depicts the trustee and provides the required data. However, misbehaving devices can perform different types of attacks and can disrupt communications for their own gain. The trustworthiness management techniques have to solve the essential issue to detect which channel is affected by malicious behaviours and so lead the nodes to successful collaboration. In particular, we proposed a trust management model, based on experience and recommendations, able to assist wireless nodes in channel selection. This appraoch does not demand any change in the standard. The different behaviors of jamming attacks have been considered and analyzed and we proposed a new one, to test the resiliency of the our proposed trust-based approach. The approaches considered above, make clear the need of a consistent organization and classification of the different types of attacks in wireless systems, that are increasing in terms of types and become more and more evolved. This categorization of attacks has been the core of 16
8.2 Non conventional communication paradigms
Participants: Valeria Loscri.
8.2.1 Visible Light Communication (VLC)
It is a well recognized matter of fact that the Internet of Everything (IoE) paradigm main limitation is represented by the exiguous wireless resources. In the last decade, Optical Wireless Communication Systems (OWCSs) have risen as a green and effective solution to alleviate the spectral scarcity and boost the ubiquitous deployment and usage of IoE devices. The significant advances in optoelectronic technology have made Light Emitting Diodes (LEDs) and photodetectors (PDs) inexpensive, and efficient hardware to equip optical transceivers. Furthermore, the emission of LEDs can be conveniently managed to provide the illumination service jointly with wireless connectivity. One of the key features of OWCSs is they are Intensity-Modulation/Direct-Detection (IM/DD) systems, requiring high energy efficient modulation techniques. Among the different modulation schemes, one of the most widespread is On-Off Keying (OOK), as a special case of Pulse-Amplitude Modulation (PAM) employing only two transmit signal power levels, one of which is set to zero. In general, even though PAM is very suitable for OWCSs, its main issue is related to the growth of the electrical/optical energy per bit, with the increase of modulation order, necessary to guarantee a certain Bit Error Rate (BER). A higher level of energy efficiency can be achieved with the adoption of orthogonal modulation schemes, although with a negative impact on spectral efficiency. Frequency-Shift Keying (FSK) belongs to the orthogonal modulation schemes category. Its main drawback in the context of OWCSs is represented by its bipolar characteristics, however the variant of FSK based on Direct-Current (DC) offset, namely DC-FSK, allows to obtain a scheme compatible with the IM/DD approach.
Based on these premises, it is clear that each modulation scheme has its own strengths and weaknesses. Hence, combining different techniques would be a promising approach to capitalize on the benefits and mitigate drawbacks. This is the main subject investigated in 15. The main novelty of this work is that we propose a multi-modulation scheme relying on the combination of non-orthogonal PPM, PAM and FSK to leverage the specific features and smartly mitigate the main drawbacks of each modulation. Such popular schemes are merged in a whole, novel framework, in order to efficiently exploit the time, amplitude and frequency features of the different schemes. The goal is to achieve performance improvements in terms of spectral and power efficiency with respect to pure modulations, providing also a constant illumination level that represents a fundamental requirement in real-world indoor VLC systems.
8.2.2 Reconfigurable Intelligent Metasurfaces
In recent years, mmWave technology has acquired an increasing interest to be exploited in future wireless cellular communications, such as in the sixth generation (6G) network scenarios. Due to the large bandwidth, very high data rates in the order of gigabit per second (Gbps) are expected to be achieved with much increased capacity, as compared to other existing wireless communication systems. Furthermore, since mmWave links present high directionality feature, an efficient spatial and frequency reuse can be obtained, with the possibility to exploit Line-of-Sight (LOS) links that are very beneficial for interference control. However, some important issues related to the specific propagation features of mmWave signal need to be considered and addressed in order to exploit the enormous potentiality of this technology. Among the main challenges with mmWave we remind the significant path loss that the mmWave signals experience, the blockage due to obstacles, the atmospheric attenuation, as well as harsh weather conditions such as rain, absorption by water vapors, and oxygen, that degrade the mmWave channel. Recently, in order to address the main issues of mmWaves technology, the concept of Reconfigurable Intelligent Meta- Surface has been introduced in the research community. Concerning the optimization of RIM-based systems, previous contributions in literature have regarded the feasibility to achieve beamforming based on RIM exploitation, by proposing optimization approaches. Other approaches have been proposed to relax the associated feedback overhead and are mostly based on statistical Channel State Information (CSI) and still relay on channel-state and on channel control to steer the RIM beams. In 13, the main aim is to relax the control channel and the high overhead associated to, by exploiting a pre-existing and well-deployed infrastructure, namely the cameras that are nowadays mas- sively deployed in the modern cities. Basically, we exploit the concept of View to Communicate V2C, by means of a CV- based approach to monitor traffic load in a real network scenario. The CV solution is introduced together with a RIM-based sub-system, performing beam steering func- tionality in the mmWave working frequency. The developed framework, BEST-RIM is evaluated by the means of Monte-Carlo approach, and the impact of the Computer Vision as well as the Genetic Algorithm integrate in the appraoch and used to compute the most suitable solution are evaluated. In 26 we also consider a mmWave RIM-based infrastructure, but we better focus on beem-steering capabilityes. In particular, we propose a novel reconfigurable intelligent metasurface able to perform beam-steering in mmWave frequencies. It has the advantage to be insensitive to the angle of incidence up to 75◦. The control of the direction of beams generated by the metasurface towards a target receiver, is realized by the means of a Particle Swarm Optimization (PSO) algorithm. Finally, our metasurface is placed inside a system including a base station and a mobile receiver and the impact of the interferers on the ability of the metasurface of tracking the user is evaluated.
8.3 Data and data-based knowledge extraction for networking
Participants: Jana Koteich, Nathalie Mitton, Nina Santi.
The ubiquity of mobile devices equipped with radio communication technologies has made large-scale data collection on human mobility commonplace. Therefore, with the lack of datasets, data collection and publication are raising new scientific questions. This is why we developed the PILOT dataset and its privacy-preserving data collection methodology for wireless communication technologies 28. The dataset is a collection of four pieces of information collected together in different mobility contexts. It includes three wireless communication technologies: WiFi beacons, Bluetooth Low Energy (BLE) beacons and Long Range Radio (LoRa) packets, as well as additional information that includes: Acceleration, Roll and Pitch, all collected at the same time. We provide the keys to replicate this data collection. The dataset is collected for about 60 hours, with a size of 150 MB using Pycom's FiPy devices and is uploaded to GitHub. We believe that the combination of the different types of information collected in different mobility scenarios constitutes a new generation of a rich dataset.
We then leverage this dataset to propose a new approach for mobility classification using a real dataset of WiFi and BLE beacons collected over one year for around 90 hours in different scenarios and conditions 24. The first model (B-model) aims to identify the status of a device if stationary or mobile. Then a complementary model (M-model) is applied to determine a more precise real-life situation of the device, which could be a Home, Office, Bus, Train, etc. The results show that decision- tree-based ensemble ML algorithms like LGBMClassifier and XGBClassifier gave the best results, in terms of accuracy and f1 score for both models with an accuracy of 99% and 94% respectively, confirming the capability of classifying mobility context from only WiFi and BLE data. We believe that such an approach could be leveraged for studying human mobility and an important step towards the large deployment of mobility-based applications by leveraging everyday mobile phones.
8.4 Digital agriculture
Participants: Carol Habid, Adriana Arteaga Arce, Jana Koteich, Nathalie Mitton, Damien Wohwe Sambo.
There exist several ways to reduce energy consumption in wireless sensor networks in general and in particular for digital agriculture applications. We have focused on data reduction approach, relying on the observation that agriculture data can be correlated or easyly estimated. The lead idea being that if two phenomena are correlated, then maybe we could estimate the way one goes based on the way the second one do. This effectively reduces the amount of data nodes may have to transmit while preserving the information.
In 12, we introduce two mechanisms to reduce the overall number of frames sensed and sent to the sink. The first approach is applied on each sensor node, where the FRABID algorithm, a joint data reduction, and frame rate adaptation on sensing and transmission phases mechanism is introduced. This approach reduces the number of sensed frames based on a similarity method. The aim is to adapt the number of sensed frames based on the degree of differ- ence between two consecutive sensed frames in each period. This adaptation technique maintains the accuracy of the video while capturing frames holding new information. This approach is validated through simulations using real data-sets from video sensors. The results show that the amount of sensed data is reduced by more than 70% compared to a recent algorithm while guaranteeing the detection of all the critical events at the sensor node level. The second approach exploits the Spatio-temporal correlation between neighboring nodes to reduce the number of captured frames. For that purpose, Synchronization with Frame Rate Adaptation SFRA algorithm is introduced where overlapping nodes capture frames in a synchronized fashion every N-1 periods, where N is the number of overlapping sensor nodes. The results show more than 90% data reduction, surpassing other techniques in the literature at the level of the number of sensed frames by 20% at least.
Then, we have proposed in 23 a similar method, but here not only limited to a pair of nodes. With our scheme we can reduce the traffic of several nodes over a whole multihop route of communications in a network. We have implemented that scheme and experimented with real hardware which shows good results.
Finally, we focused on a Wireless Underground Sensor Network (WUSN) 19 for agriculture, where challenges arise from signal attenuation in the soil and the limited battery that powers the sensor nodes. Due to the attenuation of the signal in the ground, the reception or loss of the sent data depends on the ground conditions, which can change dynamically. However, in existing WUSNs, each node sends the data collected in each round regardless of the signal attenuation. It is well demonstrated that sensor nodes consume the most energy during transmission. Obviously, transmission without receiving any data signifiicantly reduces the lifetime of a sensor node useless. This paper presents a novel fuzzy-based decision-making solution called FuzDeMa that reduces energy consumption by anticipating data losses before transmission. To do so, FuzDeMa assesses in real time the loss or the reception of a packet according to the in-situ node's environments before its transmission and decides whether to send or not the packet based on the computed reliability. To validate the proposed approach, we embed it into a dedicated underground node called the MoleNet and realized real experimentations firstly with an existing dataset and secondly, with precision-measuring equipment to estimate the energy consumption. The results revealed the possibility of prolonging the lifetime of the sensor node by saving up to 81.7876 microJ in a single round. Additionally, FuzDeMa shows the ability to save energy for up to 46 of additional revolutions, thus extending the life of the sensor node to 32.85% for 140 real transmission cycles. An analytical generalization of FuzDeMa is provided regardless of a specific dataset or sensor node. Thus, we provided the conditions for a random dataset to save the energy with any sensor node that implements FuzDeMa during transmissions.
8.5 Vehicular communications
Participants: Bingying Wang, Nathalie Mitton, Valeria Loscri.
The connected vehicle is becoming a reality, and both centralised applications provided through telecommunication infrastructure, and cooperative applications achieved directly by the vehicles through vehicle-to-vehicle communications are gaining a lot of interest from the public. Though several solutions have been investigated to ensure identification and privacy protection of vehicles participating in these applications, only a few works address the recording of exchanged messages from an audit perspective, especially in the context of vehicle-to-vehicle communications only. Therefore we have proposed a review of the literature on vehicular communications 20, and explores particularly the solutions envisaged for audit in this context, such as the Blockchain technology. We also point out the most challenging issues that should be addressed in order to achieve an effective deployment of this latter in vehicular communications, especially in the vehicle-to-vehicle communication context, which should help in developing an effective Blockchain-based audit strategy.
Broadcasting is an important routing strategy for message delivery in a VANET. However, the broadcast storm caused by loads of duplicate data packets can be severe, which leads to intense contention among vehicle nodes and a large number of dropped packets. In this case, the efficiency of message delivery is limited. In 27 we consider a broadcast routing protocol specially designed for urban areas with dense traffic and a huge amount of data traffic, and proposes a Preferred-Zone based broadcast (PreZcast) protocol. To alleviate the broadcast storm and improve the efficiency of message delivery, PreZcast only allows neighbors located within a Preferred Zone (PreZ) of a source node to rebroadcast a received packet. The PreZ is chosen based on the initial location and the distribution of two-hop neighbors of the source node. To further validate PreZcast in a more realistic and irregular topology, we evaluate PreZcast with real datasets issued from Bologna road traffic. Moreover, MultiPoint Relay (MPR) is introduced to further reduce duplicate packets in the network. Simulation results show that as compared with the Flooding protocol, PreZcast approximately improves 15% of broadcast efficiency and reduces 65% of packets transmitted with 5% more energy consumption, while PreZcast with MPR improves 10% of broadcast efficiency and reduces 70% of packets transmitted with only 0.5% more energy consumption.
In a similar approach, we have proposed an Intra-Platoon Cooperative Resource Selection (InP-CRS) scheme for frequency-time resource selection to support reliable intra-platoon message delivery 18. The proposed InP-CRS scheme is based on the standardized sensing-based semi-persistent scheduling (SPS) scheme designed for C-V2X mode 4 and is intended to address the hidden-node problem in intra-platoon communication. Specifically, the InP-CRS scheme introduces an intra-platoon cooperative mechanism, in which the last member of a platoon needs to reports the frequency-time resource occupation information of the platoon's hidden nodes to the platoon leader (PL) so that the PL can exclude those resources occupied by the hidden nodes of the platoon during its resource selection. In this way, potential packet collisions caused by the hidden nodes of a platoon can be largely reduced. Simulation results show that the proposed InP-CRS scheme can effectively improve the reliability of intra-platoon message delivery in terms of the successful broadcast probability of a PL as compared to the standardized sensing-based SPS scheme.
Obstacle detection is a tool adopted in vehicular safety applications, aiming to detect a moving obstacle in an area of interest with the highest accuracy. Different sensors are used for this aim, such as LiDAR devices mounted on board of a vehicle that capture images of the surrounding environment. Extending the number of LiDAR sensors can be useful to improve the obstacle detection accuracy, since multiple images are captured from different distances and directions, and this represents an interesting approach, specially in case of dense networks with cooperative nodes. In 11, we present MuSLi technique, aiming to (i) provide an accurate obstacle detection and (ii) forward alert messages to other cars in the network, in case of correct detection of a pedestrian crossing the street. MuSLi relies on the connected content islands scenario, where each vehicle defined as a content island subscribes to a service in order to receive and share published messages. Specifically, the road safety service allows the detection of an obstacle through multiple LiDAR sensors from neighboring cars. Furthermore, we investigate the fastest transmission mode among those defined in the C-V2X releases to alert the presence of a pedestrian to the other approaching cars. The proposed technique provides the distances by the crossroad in which is better to use V2V, V2I or V2N according to the environment, the scheduling technique and the measured interference.
Social features are affecting different application areas, from traditional online social networks to economical networks, as well as the study of epidemical behaviors of pandemics and diseases. From the information point of view, also the Internet paradigm has been revised according to social behaviors of nodes, showing intrinsic properties that have allowed the definition of the Social Internet of Things paradigm. Furthermore, considering vehicular networks, social features have been spreading their influence, and defined the concept of Vehicular Social Networks, where mobile nodes show predictable social behavior. In this context, all the networking concepts should be updated accordingly, taking into account node social aspects and interactions. In 17, we discuss the open challenge of how we should define a trust vehicle, relying on social networking aspects. We introduce the concept of node trustworthiness in a vehicular environment, based on the reputation degree, computed according to real-time interactions and past data. A node can be defined as trusted if exhibiting an acceptable reputation degree, and being successfully able to transmit data packet in a given environment. The framework of a network architecture for the computation of node trustworthiness degree in a vehicular scenario is also presented.
8.6 Leveraging BLE
Participants: Etienne Profit, Nathalie Mitton, Damien Wohwe Sambo.
Contact Tracing (CT) is an old, recognized epi- demiological tool, and since a digital variant is now within reach, a variety of smartphone-based solutions have been rapidly developed and deployed since 2020, with mixed results and amid controversies. Yet, achieving reliable and effective digital CT at large scale is still an open problem. In 25, we contribute with an open source software platform on top of which various CT solutions can be quickly developed and tested. More specifically, we design PEPPER, which jointly leverages Bluetooth Low Energy (BLE) and Ultra Wide Band (UWB) radios for contact detection, combined with the DESIRE privacy-preserving CT protocol. We show that PEPPER+DESIRE can operate on cheap physical tokens based on low-power microcontrollers, opening new use-cases with less personal, potentially disposable devices, that could be more widely used. We also evaluate the complementarity of Bluetooth and UWB in this context, via experiments mimicking various scenarios relevant for CT. Compared to BLE-only CT, we show that UWB can decrease false negatives (e.g., in presence of human body occlusion), meaning that more actual contacts will be found, a key benefit from an epidemiological viewpoint. Our results suggest that, while PEPPER+DESIRE improves precision over state-of-the-art, further research is required to harness UWB-BLE synergy for CT in practice. To this end, our open source platform (which can run on an open-access testbed) provides a useful playground for the research community.
In wireless sensor networks, much energy is wasted during connecting and control processes. This is particularly true for the neighborhood discovery process carried out in Bluetooth Low Energy (BLE) before the communications between devices. However, the fixed duration of this process has a critical energy cost when the number of neighbors is low or when only a few neighbors are required by the application. In order to address this issue, we proposed a novel protocol called WUBBLE 22 to leverage wake-up radio technology to start and end the discovery process. Wake-up radio enables additional communications between devices with an ultra-low energy overhead. WUBBLE is validated by combining analytical analysis and experimental measurements, and results show that half of the energy could be gained to discover 90% of the neighbors.
9 Partnerships and cooperations
9.1 International initiatives
9.1.1 Associate Teams in the framework of an Inria International Lab or in the framework of an Inria International Program
AGRINET
Participants: Jana Koteich, Nathalie Mitton, Damien Wohwe Sambo.
-
Title:
Wireless accurate monitoring for a smarter agriculture
-
Duration:
2021 - 2025
-
Partners :
Stellenbosch University (South Africa)
-
Inria contact:
Nathalie Mitton
-
Summary:
The proposed research entails the development of a flexible, rapidly deployable, biological data acquisition platform to create advanced agricultural monitoring and management techniques for better natural resource management and smart farming decision making. This platform will involve a wireless sensor network and a machine-learning based decision making tools. Sensors will be spread over the fields to sense information on soil water and nitrate concentration, temperature etc, and remotely communicate this data in a wireless way to the server which will provide decision making tools according to the kind of culture. A first objective is to create an advanced, flexible wireless sensor network for wide area agricultural data measurement, with an adaptable dynamic routing strategy including the considerations of various factors such as network availability, node positioning, message priority and resource availability (typically battery capacity) in order to optimize data transmission reliability and utilize communication resources optimally. This particular topology is proposed to enhance the total network coverage and to compensate for propagation problems that are certain to occur due to the variable crop-, climatic- and vineyard topography. A second objective to be achieved in parallel is to adapt current machine learning and pattern recognition algorithms to obtain an area wide and in depth view of crop and soil conditions to identify and enable optimal crop management and harvest conditions. In AgriNet, multiple inputs from multiple nodes will be integrated into a machine learning based classification framework. Complementary and inter-dependent data input will enable and enhance the detection of converging patterns, providing a completely new level of confidence in terms of early warning strategies and sensing accuracy. This could be of enormous value in presenting early warning signs of disease and other unwanted conditions for cost efficiency and increase in crop yield and quality. A third objective is the integration of the final system (wireless sensor network and machine learning based system) in a complete agriculture-oriented prototype. Pilot projects will be deployed during the last year in both France and South Africa focusing on two main cultures: potato crops and vineyards in order to stress and evaluate the AgriNet prototype.
9.2 International research visitors
9.2.1 Visits of international scientists
Riaan Wolhuter spent one week at Inria from Stellenbosch University in September 2023.
Hervé Oulu spent three months at Inria from University of Benin as a visiting PhD student.
Gerardo Hernandez Oregon from Instituto Politécnico Nacional de Mexico spent 6 months at Inria FUN.
9.2.2 Visits to international teams
Research stays abroad
Participants: Jana Koteich.
-
Visited institution:
Stellenbosch University
-
Country:
South Africa
-
Dates:
March 15 - May 15 2023
-
Context of the visit:
In the framework of the Agrinet project.
Participants: Ildi Alla.
-
Visited institution:
Irvine University
-
Country:
USA
-
Dates:
October 1 - December 31 2023
-
Context of the visit:
in the framework of DEPOSIA project
9.3 European initiatives
9.3.1 Horizon Europe
NEPHELE
Participants: Adriana Arteaga Arce, Hazem Chaabi, Carol Habid, Nathalie Mitton.
NEPHELE project on cordis.europa.eu
-
Title:
A LIGHTWEIGHT SOFTWARE STACK AND SYNERGETIC META-ORCHESTRATION FRAMEWORK FOR THE NEXT GENERATION COMPUTE CONTINUUM
-
Duration:
September 2022 - August 2025
-
Inria contact:
Nathalie Mitton
-
Summary:
The vision of NEPHELE is to enable the efficient, reliable and secure end-to-end orchestration of hyper-distributed applications over programmable infrastructure that is spanning across the compute continuum from Cloud-to-Edge-to-IoT, removing existing openness and interoperability barriers in the convergence of IoT technologies against cloud and edge computing orchestration platforms, and introducing automation and decentralized intelligence mechanisms powered by 5G and distributed AI technologies.
The NEPHELE project aims to introduce two core innovations, namely:
(i) an IoT and edge computing software stack for leveraging virtualization of IoT devices at the edge part of the infrastructure and supporting openness and interoperability aspects in a device-independent way. Through this software stack, management of a wide range of IoT devices and platforms can be realised in a unified way, avoiding the usage of middleware platforms, while edge computing functionalities can be offered on demand to efficiently support IoT applications’ operations.
(ii) a synergetic meta-orchestration framework for managing the coordination between cloud and edge computing orchestration platforms, through high-level scheduling supervision and definition, based on the adoption of a “system of systems” approach.
The NEPHELE outcomes are going to be demonstrated, validated and evaluated in a set of use cases across various vertical industries, including areas such as disaster management, logistic operations in ports, energy management in smart buildings and remote healthcare services. Two successive open calls will also take place, while a wide open-source community is envisaged to be created for supporting the NEPHELE outcomes.
SLICES-PP
Participants: Lucille Colin, Solenne Fortun, Nathalie Mitton.
-
Title:
Scientific Large-scale Infrastructure for Computing/Communication Experimental Studies - Preparatory Phase
-
Duration:
September 2022 - December 2025
-
Inria contact:
Nathalie Mitton
-
Summary:
The digital infrastructures research community continues to face numerous new challenges towards the design of the Next Generation Internet. This is an extremely complex ecosystem encompassing communication, networking, data-management and data-intelligence issues, supported by established and emerging technologies such as IoT, 5/6G, cloud-to-edge computing. Coupled with the enormous amount of data generated and exchanged over the network, this calls for incremental as well as radically new design paradigms. Experimentally-driven research is becoming worldwide a de-facto standard, which has to be supported by large-scale research infrastructures to make results trusted, repeatable and accessible to the research communities.
SLICES-RI (Research Infrastructure), which was recently included in the 2021 ESFRI roadmap, aims to answer these problems by building a large infrastructure needed for the experimental research on various aspects of distributed computing, networking, IoT and 5/6G networks. It will provide the resources needed to continuously design, experiment, operate and automate the full lifecycle management of digital infrastructures, data, applications, and services.
Based on the two preceding projects within SLICES-RI, SLICES-DS (Design Study) and SLICES-SC (Starting Community), the SLICES-PP (Preparatory Phase) project will validate the requirements to engage into the implementation phase of the RI lifecycle. It will set the policies and decision processes for the governance of SLICES-RI: i.e., the legal and financial frameworks, the business model, the required human resource capacities and training programme. It will also settle the final technical architecture design for implementation. It will engage member states and stakeholders to secure commitment and funding needed for the platform to operate. It will position SLICES as an impactful instrument to support European advanced research, industrial competitiveness and societal impact in the digital era.
MLSysOps
Participants: Aya Moheddine, Valeria Loscri, JiaLi Xi.
-
Title:
Machine Learning for Autonomic System Operation in the Heterogeneous Edge-Cloud Continuum
-
Duration:
January 2023 - December 2025
-
Inria contact:
Valeria Loscri
-
Summary:
MLSysOps will achieve substantial research contributions in the realm of AI-based system adaptation across the cloud-edge continuum by introducing advanced methods and tools to enable optimal system management and application deployment. MLSysOps will design, implement and evaluate a complete framework for autonomic end-to-end system management across the full cloud-edge continuum. MLSysOps will employ a hierarchical agent-based AI architecture to interface with the underlying resource management and application deployment/orchestration mechanisms of the continuum. Adaptivity will be achieved through continual ML model learning in conjunction with intelligent retraining concurrently to application execution, while openness and extensibility will be supported through explainable ML methods and an API for pluggable ML models. Flexible/efficient application execution on heterogeneous infrastructures and nodes will be enabled through innovative portable container-based technology. Energy efficiency, performance, low latency, efficient, resilient and trusted tier-less storage, cross-layer orchestration including resource-constrained devices, resilience to imperfections of physical networks, trust and security, are key elements of MLSysOps addressed using ML models. The framework architecture disassociates management from control and seamlessly interfaces with popular control frameworks for different layers of the continuum. The framework will be evaluated using research testbeds as well as two real-world application-specific testbeds in the domain of smart cities and smart agriculture, which will also be used to collect the system-level data necessary to train and validate the ML models, while realistic system simulators will be used to conduct scale-out experiments. The MLSysOps consortium is a balanced blend of academic/research and industry/SME partners, bringing together the necessary scientific and technological skills to ensure successful implementation and impact.
9.3.2 Other european programs/initiatives
Druid-Net
Participants: Adriana Arteaga Arce, Carol Habid, Nathalie Mitton, Nina Santi.
-
Title:
eDge computing ResoUrce allocatIon for Dynamic NETworks
-
Duration:
May 2020 - September 2023
-
Inria contact:
Nathalie Mitton
-
Summary:
Following the NFV/SDN paradigm, DRUID-NET separates the flow of information into control and data plane. At the lowest layer, the IoT-enabled applications are deployed, and the generated workload (data flow) can be offloaded for further processing at the above EC layer, which provides essential virtualized services. The DRUID-NET framework collects information (control flow) about the status of the computing and network infrastructure at the EC level in order to create workload-resource profiles, update the performance model for every application, and realize the feedback control mechanism for the resource allocation and simultaneously implements a resource-aware control strategy for the CPS to be controlled (control flow). This holistic approach allows the application’s dynamical modelling taking into account various contextual information. Furthermore, the controller co-design treats the resource allocation algorithms as application components in the virtualized services.
NEWFOCUS
Participants: Valeria Loscri.
-
Title:
European network on future generation optical wireless communication technologies
-
Duration:
September 2020 - September 2024
-
Inria contact:
Valeria Loscri
-
Summary:
The COST Action NEWFOCUS will propose truly radical solutions with the potential to impact the design of future wireless networks. Particularly, NEWFOCUS aims to establish optical wireless communications (OWC) as an efficient technology that can satisfy the demanding requirements of backhaul and access network levels in beyond 5G networks. This also includes the use of hybrid links that associate OWC with radiofrequency or wired/fiber-based technologies. Towards this vision, NEWFOCUS will carry out a comprehensive research programme under two major pillars. The first pillar is on the development of OWC-based solutions capable of delivering ubiquitous, ultra-high-speed, low-power consumption, highly secure, and low-cost wireless access in diverse application scenarios. The developed solutions will in particular support Internet-of-Things (IoT) for smart environments with applications in vertical sectors. The second pillar concerns the development of flexible and efficient backhaul/fronthaul OWC links with low latency and compatible with access traffic growth.
BeingWise
Participants: Valeria Loscri.
-
Title:
Behavioral Next Generation in Wireless Networks for Cyber Security (BEiNG-WISE)
-
Duration:
2023 - 2027
-
Action Chair and Scientific Holder:
Valeria Loscri
-
Summary:
The always-connected world we are living in, gives us an unprecedented plethora of new advanced services and automated applications requiring, more and more, less human intervention due to the increased integration of Machine Learning (ML), Artificial Intelligence (AI) approaches and sophisticated emerging wireless technologies.
On the other side, this connected world opens new breaches and creates new potential vulnerabilities for smart advanced cyber-attacks, namely attacks and offender relying on ML/AI and advanced wireless technology integration, to make their attack more effective and less detectable. If an increasing awareness by the users could help to contrast the security issues, it is not sufficient against the new generation of cyber-attacks. In this context, a drastic paradigm shift, putting human-being in the loop for the conception of novel and more effective cyber-security solutions, must be considered.
Human-beings have a double role in the cyber-connected world: as potential offender and potential victim. The focus of BEiNG-WISE will be on how these different human-being features can be combined with the advanced technological characteristics, in order to conceive non-conventional, responsible by design, cyber-security solutions accounting for both these factors. In this complex connected system, another fundamental aspect that needs to be accounted to, is the legal one, related to the conception of solutions that can be effectively employed in the real world. Also, legal aspects should be considered at the design stage. The Action relies on cross-domains expertise, ranging from cybersecurity, wireless communication technology, data science, sociology, psychology and law.
9.4 National initiatives
GoodFloow
Participants: Damien Wohwe Sambo, Nathalie Mitton.
-
Title:
ADEME GoodFloow Project
-
Duration:
October 2021 - September 2023
-
Coordinator:
GoodFloow
-
Inria contact:
Nathalie Mitton
-
Summary:
The goal of this project, funded by ADEME, is to design a very energy efficient node to manage reusable packaging in a more sustainable way by combining enhanced IA techniques, wake up radio and multi MAC layers.
AutonomousPack
Participants: Damien Wohwe Sambo, Nathalie Mitton.
-
Title:
ADEME Autonomous Pack Project
-
Duration:
September 2023 - August 2026
-
Coordinator:
GoodFloow
-
Inria contact:
Nathalie Mitton
-
Summary:
The goal of this project, funded by ADEME, is to design a very energy efficient node to manage reusable packaging in a more sustainable way by combining enhanced IA techniques, wake up radio and multi MAC layers.
DEPOSIA
Participants: Valeria Loscri.
-
Title:
Detection and geolocation of an illegitimate electromagnetic source with AI
-
Duration:
October 2021 - September 2024
-
Coordinator:
Virginie Deniau
-
Inria contact:
Valeria Loscri
-
Summary:
The ANR project DEPOSIA focuses on the detection and geolocation of various radio frequency signal sources in order to thwart attacks on connected systems and infrastructures. The sources considered are elements which by their characteristics or their position, present an illicit character and which threaten the people security or the infrastructures. For outdoor cases, we consider drones flying over forbidden areas, telecommunication jammers, spoofing signal transmitters or wireless connected sensors used to introduce false data in monitoring platforms. For indoor cases, we also consider jamming or spoofing sources that can cause denial of service within networks or infrastructures, or fake access points that aim to carry out man-in-the-middle attacks to intercept information. In this proposal, the indoor and outdoor use cases are considered separately in order to design monitoring infrastructures adapted to each case. For the outdoor case, we consider a surveillance architecture that could join the already existing cellular or WLAN communication infrastructures. In particular, with 5G technology and the higher employed frequencies, cellular networks are evolving towards finer meshes and have interfaces with the core network at each of their nodes. Thus, these interface points, equipped with receivers dedicated to monitoring, could enable the routing of monitoring data to centralized platforms, feeding an Artificial Intelligence for analysis, anomaly detection and source geolocation. For the indoor case, we consider a distributed monitoring architecture deployed within a building, based on SDR sensors and a data centralization and synchronization network. In these two cases, we envisage an Artificial Intelligence working on data evolving in three dimensions : time, space and direction, all for data of different natures, namely those from the physical layer and the data link layer. Whether for indoor or outdoor configurations, the algorithms that will constitute the Artificial Intelligence will be based on learning approaches that will correspond to Machine Learning and Deep Learning algorithms. These algorithms will deal with the problems of detecting attacks and locating illicit sources. These algorithms will have to take into account: the evolutionary aspect brought by the non-fixed character in time of the attacks and the non-fixed location aspect of the localization of the source of the attack. A first Artificial Intelligence will be dedicated to data analysis and anomaly detection, i.e., highlighting the suspicious nature of the data, and a second Artificial Intelligence will be dedicated to extracting the location information of the attack source. Due to the multi-layered nature of the data, model aggregation algorithms will be deployed in order to homogenize the decision process.
ROAD-AI, common DEFI Inria and Cerema
Participants: Nathalie Mitton.
-
Title:
Routes et ouvrages d'art Diversiformes, Augmentés et intégrés
-
Duration:
July 2021 - June 2024
-
Inria contact:
Nathalie Mitton
-
Summary:
Integrated management of infrastructure assets is an approach which aims at reconciling long-term issues with short-term constraints and operational logic. The main objective is to enjoy more sustainable, safer and more resilient transport infrastructure through effective, efficient and responsible management. To achieve this, CEREMA and Inria are joining forces in this Inria Challenge (DEFI) which main goals are to overcome scientific and technical barriers that lead to the asset management of tomorrow for the benefit of road operators: (i) build a “digital twin” of the road and its environment at the scale of a complete network; (ii) define “laws” of pavement behavior; (iii) instrument system-wide bridges and tunnels and use the data in real time; (iv) define methods for strategic planning of investments and maintenance.
PEPR
The FUN team is involved in PEPR Networks of the future (PC6 and PC7), PEPR Cloud (PC8) and PEPR MobiDec (PC 3).
9.5 Regional initiatives
STIMULE CORTESE
Participants: Valeria Loscri, Selma Yahia.
-
Title:
CORTESE: Intelligent CO-existence of Communication Wireless Technologies for Secure and Intelligent applications
-
Duration:
January 2023 - December 2025
-
Inria contact:
Valeria Loscri
-
Summary:
This project led by the Inria Lille - Nord Europe center and in partnership with the Gustave Eiffel University (UGE), the LAMIH (Université Polytechnique Hauts de France (UPHF)) aims at the coexistence of different wireless communication technologies, in the vehicular context. The objective is to advance in the search for methods based on sustainable Artificial Intelligence (AI) which can automate the selection of the most relevant communication technology to improve performance in terms of latency (i.e., of the order of 1 ms), reliability (i.e., of the order of 99.99% of data delivered) in order to reduce the energy envelope of the communication system and guarantee increased robustness in the face of cyber attacks. Given the high dynamicity of the environment, the learning approaches developed must be capable of responding in real time. Particular attention will be paid to the sustainability and security aspects of wireless communication networks. This project is part of the field of embedded Artificial Intelligence and the new emerging sector of cyber security for critical systems such as the vehicular context. With a clear experimental footprint, this project will advance research in the Hauts-de-France region in 5G technology in a key sector such as Intelligent Transport.
10 Dissemination
Participants: Valeria Loscri, Nathalie Mitton.
10.1 Promoting scientific activities
General chair, scientific chair
- Valeria Loscri was organizer and chair of Social networking in Metaverse (SocMeta) Workshop, Rome 2023
- Valeria Loscri was co-organizer and chair of TRUSTNET DAY, Trust and Privacy in Networks, Avignon, June 2023
- Valeria Loscri was co-organizer and chair of 1st Workshop on Underwater Communication, Access and Networking (UCAN), in conjunction with ICC 2023
10.1.1 Scientific events: selection
Chair of conference program committees
- Valeria Loscri is Privacy and Security track chair at WF-IoT 2024, TPC co-chair of EWSN 2023, Symposium Chair of Wireless Communications Symposium, Medium access control and Networking Track chair at WCNC 2024 and Short Papers and Demo Session chair of WiMob 2023
- Nathalie Mitton was co-TPC chair of the 2023 GoodIt Special track chair and TPC co-chair of Algotel 2023. She is co-TPC chair of DCOSS 2024 and WiMob 2024 and Tuto and workshop co-chair of EWSN 2024.
Member of the conference program committees
- Valeria Loscri has been a TPC member of IEEE Infocom 2023, Percom 2023, ESORICS 2023 and 2024, IEEE CSN 2023 and 2024.
- Nathalie Mitton has been a TPC member of Infocom 2023, DCOSS 2023, Percom 2023, Globecom 2023, and WCNC 2023.
10.1.2 Journal
Member of the editorial boards
- Valeria Loscri is Associate Editor of IEEE Transactions on Information Forensics and Security (since 2022), IEEE Communications Survey and Tutorials (COMST, since 2020), Elsevier ComCom (since 2021), Frontiers in Communications and Networks, ITU-FET Journal, IEEE Transactions on Nanobioscience journal since 2017, of Elsevier Computer Networks journal since 2016, of Robotics Software Design and Engineering of the International Journal of Advanced Robotic Systems since 2016, of Elsevier Journal of Networks and Computer Applications (JNCA) journal since 2016, of Wiley Transactions Emerging Telecommunications Technologies since 2019.
- Nathalie Mitton is an editorial board member of Adhoc Networks since 2012, of IET-WSS since 2013, of Wireless Communications and Mobile Computing since 2016, of Journal of Interconnection Networks since 2021.
10.1.3 Invited talks
- Valeria Loscri was invited speaker at workshop Inria-CISPA, Paris
- Valeria Loscri was invited speaker at 8th Franco-Japanese Cybersecurity workshop, Bordeaux
- Valeria Loscri was invited keynote speaker at ENAC - Toulouse to deliver a talk on How Machine Learning is changing the Cybersecurity landscape in Wireless Communication Networks
- Valeria Loscri was invited keynote speaker at ENAC - Toulouse to deliver a talk on How Machine Learning is changing the Cybersecurity landscape in Wireless Communication Networks
- Valeria Loscri was invited keynote speaker on Machine Learning and Visible Light Communication at the Journées Scientifiques URSI - France
- Valeria Loscri was invited keynote speaker at the PhD Day - INSA Lyon, with a talk on Unconventional Wireless Communication Technologies
- Valeria Loscri invited speaker at Journée Sécurité CRISTAL, with a talk on How Machine Learning is changing the Cybersecurity landscape in Wireless Communication Networks
- Nathalie Mitton was invited keynote at November 2023 CONNECT THEM ALL session.
10.1.4 Scientific expertise
- Valeria Loscri has been appointed as Evaluator Expert for Horizon Europe KDT-JU Program and Horizon Europe 6G SNS-JU Program,
- Valeria Loscri is FWO expert panel member for the PhD fellowship-Fundamental Research and for the Postdoc fellowship-Fundamental Research.
- Nathalie Mitton has been appointed as scientific expert to evaluate projects submitted to ANR, South Africa's National Research Foundation (NRF), NSERC (Canada) and NSC (Poland).
- Nathalie Mitton is an external expert of scientific board for Inrae, IRIT lab and ESISAR.
10.2 Teaching - Supervision - Juries
10.2.1 Teaching
- Master: Valeria Loscri, Objets Communicants, 24h (Mineure Habitat Intelligent), Ecole des Mines de Douai, France
- Master: Nathalie Mitton, Wireless networks, 16h eqTD (Master TC), Université de Lille, France
- Master: Damien Wohwe Sambo, Wireless sensor networks, 16h eqTD (Master IdO), Université de Lille, France
- Master: Adriana Arteaga Arce and Hazem Chaabi, Smart objects, 10h CM + 12h TP, Ecole Centrale de Lille, France
- Master: Adriana Arteaga Arce and Hazem Chaabi, Industrial Internet of Things, 10h CM, Ecole Centrale de Lille, France
- Master: Damien Wohwe Sambo, Industrial to Internet of Things, 4h Cours + 12h TP, Ecole Centrale de Lille, France
- Master: Damien Wohwe Sambo, Wireless sensor networks, 12h eqTD (Master ROC), IMT, France
10.2.2 Supervision
- PhD defended:
- Nina Santi, adaptive and dynamic edge gateways IoT-oriented deployments, Université de Lille, 2020-2023, defended on December 19, Nathalie Mitton
- PhD in progress:
- Aymen Bouferroum, vulnerability detection, trust and authentication methods applied to multi-technology communication in Industrial IoT (IIoT), Université de Lille, 2023-2026, Valeria Loscri
- Selina Cheggour, Cell-free approaches in wireless networks, Université de Lille, 2023-2026, Valeria Loscri
- Marwa Slimene, Blockchain-based security and audit for ioT and V2X communications, Université de Lille, 2023-2026, Nathalie Mitton
- Jiali Xu, anomaly and attack detection in intelligent, deep systems with heterogeneous, reprogrammable nodes, Université de Lille, 2023-2026, Valeria Loscri
- Hazem Chaabi, Adaptive deployment of a distributed wireless monitoring network and edge services using a fleet of wireless robots, Université de Lille, 2022-2025, Nathalie Mitton
- Ildi Alla, Monitoring for detection and localisation of cyber attacks in wireless networks, Université de Lille, 2022-2025,Valeria Loscri
- Jana Koteich, Context aware opportunistic forwarding strategy, Université de Lille, 2021-2024, Nathalie Mitton
10.2.3 Juries
PhD committees:
- Valeria Loscri is/was member of the following PhD thesis committees:
- Ali Haj-Hassan, University of Mons, examiner and secretary.
- Michaël Mahamat, University of Compiegne, examiner.
- Abhishek Djeachandrane, University of Paris Est, reviewer.
- Shuo Li, Centrale Supélec, reviewer
- Firmin Kateu, University of Toulouse, reviewer
- Farzad Veisi, University of Strasbourg, reviewer.
- Khaled Abid, University of Compiegne, reviewer.
- Alessandro Visentin, University of Padova, reviewer.
- Chaima Zoghlami, Universiy of Toulouse, reviewer.
- Chaimaa BOUDAGDIGUE, Univ. of Avignon, reviewer.
- Sana BENHAMAID, Univ. of Compiegne, reviewer;
- Bruno CHIANCA, ENAC, Toulouse, reviewer;
- Nathalie Mitton is/was member of the following PhD thesis committees:
- Debashisha Mishra, Lorraine university, chair
- Vishaka Basnayake, UTBM, chair
- Maysaa Khalil, UTT
- Berat Senet, Sorbonne University, reviewer
- Ichrak Mokhtari, INSA Lyon, reviewer
- Ludovic Javet, UVSQ, chair
- Hugo Hadjur, ENS Lyon, reviewer
- Jad Bassil, Univ. Bourgogne, chair
- Razanne Abu-Aisheh, Sorbonne Université, chair and reviewer
- Hadi Yakan, UVSQ, chair
- Driss Aouladhaj, UGE, chair
- Olivier Lourme, Univ. Lille
Researcher selection committees:
- Valeria Loscri is/was member of the following selection committees:
- Inria Junior Research (CR) committee for Inria Lyon
- Assistant professor: Université Côte d'Azur, Université de Toulouse
- National Secondment Committee Inria
- Nathalie Mitton was member of the following selection committees:
- Inria researcher: vice-chair of the junior researcher committee (CR) for Inria Lille and member of Senior researcher committee (DR2)
- Professor: Universités de Lorraine.
- Assistant professor: Université d'Annecy, IMT Lille Nord Europe, Sorbonne University, Université Polytechnique des Hautes de France
- CPJ : INSA Lyon, Inria Lille
10.3 Internal or external Inria responsibilities
- Nathalie Mitton
- is Deputy Scientific delegate for Lille Inria center
- is member of the QVT (Quality of life at work) committee
- is a member of the Bureau des Comités de Projets of Lille Inria center.
- is a member of the evaluation committee of Inria.
- Valeria Loscri
- is Scientific International Relation Responsible for Inria Lille.
- is Staff Representative (substitute)
11 Scientific production
11.1 Major publications
- 1 articleAdaptive Modulation Control for Visible Light Communication Systems.Journal of Lightwave TechnologyFebruary 2021HALDOI
- 2 inproceedingsAn Open Experimental Platform for Ranging, Proximity and Contact Event Tracking using Ultra-Wide-Band and Bluetooth Low-Energy.CNERT 2021 - IEEE INFOCOM Workshop on Computer and Networking Experimental Research using TestbedsVirtual, FranceMay 2021HAL
- 3 articleRODENT: a flexible TOPSIS based routing protocol for multi-technology devices in wireless sensor networks.ITU Journal on Future and Evolving Technologies21April 2021HAL
- 4 inproceedingsDenial-of-Sleep Attacks against IoT Networks.CoDIT 2019 - 6th International Conference on Control, Decision and Information TechnologiesParis, FranceApril 2019HAL
- 5 inproceedingsA Machine Learning Regression approach for Throughput Estimation in an IoT Environment.iThings-2021: The 14th IEEE International Conference on Internet of ThingsMelbourne, AustraliaDecember 2021HAL
- 6 articleOpportunistic multi-technology cooperative scheme and UAV relaying for network disaster recovery.Information111January 2020HALDOI
- 7 inproceedingsGraphene-Based Reconfigurable Intelligent Metasurface Structure for THz Communications.EuCAP 2021 - 15th European Conference on Antennas and PropagationDüsseldorf / Virtual, GermanyMarch 2021HAL
- 8 articleDesign and analysis of a reconfigurable intelligent meta-surface for vehicular networks.ITU Journal on Future and Evolving TechnologiesDecember 2020HAL
- 9 articleDIVINE: Data Offloading In Vehicular Networks with QoS Provisioning.Ad Hoc Networks123December 2021HAL
- 10 inproceedingsA VLC-based Footprinting Localization Algorithm for Internet of Underwater Things in 6G networks.IEEE 5th International Workshop on Optical Wireless Communications (IWOW)Berlin, GermanySeptember 2021HAL
11.2 Publications of the year
International journals
International peer-reviewed conferences
National peer-reviewed Conferences
11.3 Cited publications
- 29 inproceedingsAutomated and Reproducible Application Traces Generation for IoT Applications.Q2SWinet 2021 - 17th ACM Symposium on QoS and Security for Wireless and Mobile NetworksAlicante, SpainACMNovember 2021, 1-8HALDOIback to text
