Section: Application Domains
Computations and Dynamical Systems
Continuous computation theories
Understanding computation theories for continuous systems leads to studying hardness of verification and control of these systems. This has been used to discuss problems in fields as diverse as verification (see e.g. [33] ), control theory (see e.g. [40] ), neural networks (see e.g. [71] ), and so on.
We are interested in the formal decidability of properties of dynamical systems, such as reachability [61] , the Skolem-Pisot problem [36] , the computability of the -limit set [60] . Those problems are analogous to verification of safety properties.
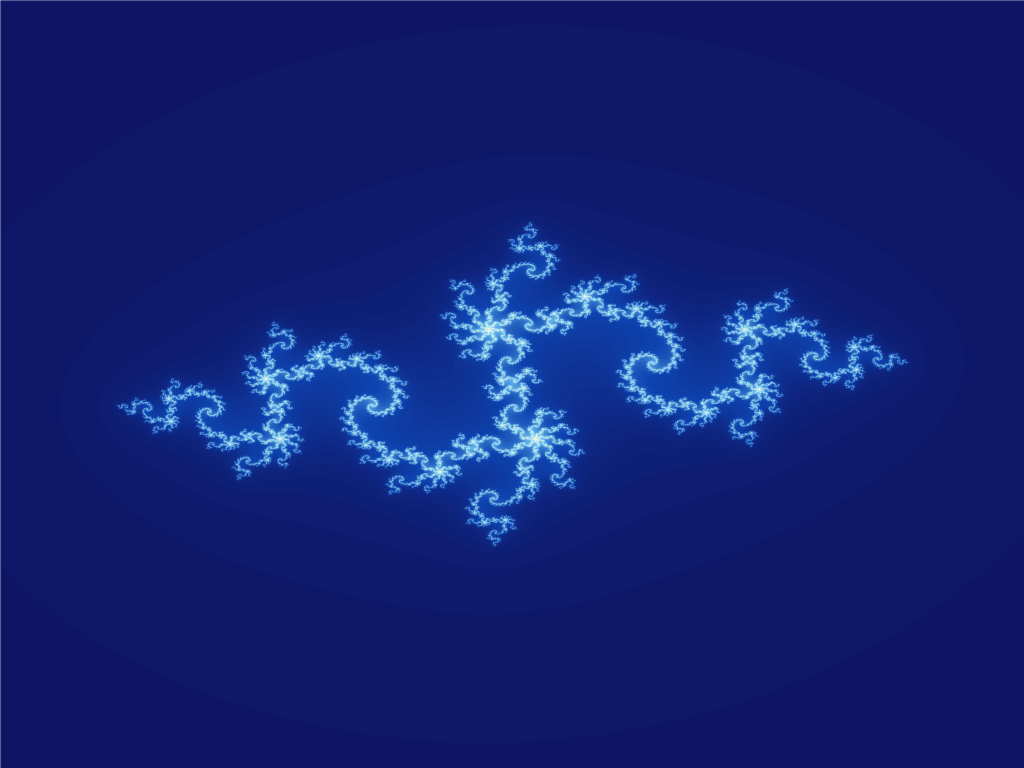
Due to the difficulty of their analysis, the study of dynamical systems is often impossible without computer simulations. Nevertheless those simulations are often heuristic and due to round-off errors, what is observed on the screen is not guaranteed to reflect the actual behavior of the original mathematical system. Computable analysis has the advantage of getting rid of the truncation problems, integrating the management of errors to the computation. We then use this theory to investigate the possibility to compute characteristics of dynamical systems that are fundamental objects in the mathematical theory, such as attractors or invariant measures. Being asymptotic objects, they might not be always computable: for instance it has been proved in [41] that some Julia sets (see Figure 1 ) cannot be computed at all, i.e. there is no program that would plot such sets up to any resolution.
In [18] we prove that there exist computable systems for which the statistical long-term behavior (technically the invariant measures) is not computable.
In contrast with the discrete setting, it is of utmost importance to compare the various models of computation over the reals, as well as their associated complexity theories. In particular, we focus on the General Purpose Analog Computer of Claude Shannon [72] , on recursive analysis [78] , on the algebraic approach [68] and on computability in a probabilistic context [63] .
A crucial point for future investigations is to fill the gap between continuous and discrete computational models. This is one deep motivation of our work on computation theories for continuous systems.
Analysis and verification of adversary systems
The other research direction on dynamical systems we are interested in is the study of properties of adversary systems or programs, i.e. of systems whose behavior is unknown or indistinct, or which do not have classical expected properties. We would like to offer proof and verification tools, to guarantee the correctness of such systems.
On one hand, we are interested in continuous and hybrid systems. In a mathematical sense, a hybrid system can be seen as a dynamical system, whose transition function does not satisfy the classical regularity hypotheses, like continuity, or continuity of its derivative. The properties to be verified are often expressed as reachability properties. For example, a safety property is often equivalent to (non-)reachability of a subset of unsure states from an initial configuration, or to stability (with its numerous variants like asymptotic stability, local stability, mortality, etc ...). Thus we will essentially focus on verification of these properties in various classes of dynamical systems.
We are also interested by rewriting techniques, used to describe dynamic systems, in particular in the adversary context. As they were initially developed in the context of automated deduction, the rewriting proof techniques, although now numerous, are not yet adapted to the complex framework of modelization and programming. An important stake in the domain is then to enrich them to provide realistic validation tools, both in providing finer rewriting formalisms and their associated proof techniques, and in developing new validation concepts in the adversary case, i.e. when usual properties of the systems like, for example, termination are not verified.
For several years, we have been developing specific procedures for property proofs of rewriting, for the sake of programming, in particular with an inductive technique, already applied with success to termination under strategies [52] , [53] , [54] , to weak termination [55] , sufficient completeness [57] and probabilistic termination [56] .
The last three results take place in the context of adversary computations, since they allow for proving that even a divergent program, in the sense where it does not terminate, can give the expected results.
A common mechanism has been extracted from the above works, providing a generic inductive proof framework for properties of reduction relations, which can be parametrized by the property to be proved [58] , [59] . Provided program code can be translated into rule-based specifications, this approach can be applied to correctness proof of software in a larger context.
A crucial element of safety and security of software systems is the problem of resources. We are working in the field of Implicit Computational Complexity. Interpretation based methods like Quasi-interpretations (QI) or sup-interpretations, are the approach we have been developing these last five years, see [65] , [66] , [67] . Implicit complexity is an approach to the analysis of the resources that are used by a program. Its tools come essentially from proof theory. The aim is to compile a program while certifying its complexity.